Featured Insights
CMMC Compliance Consulting for Canadian Defence Contractors
Canadian companies selling into the U.S. defence supply chain face a compliance requirement that is no longer theoretical. The Cybersecurity Maturity ...
Filter by Tag
Why Waiting for the RFP Is the Costliest Compliance Plan
Most companies treat compliance as a procurement problem. Something to handle when a customer or a contract surfaces it. The logic is reasonable on...
Security Vendors With Strong Practices and No Documentation
Here is a contradiction I run into constantly.
A security software vendor calls for a SOC 2 readiness conversation. We start poking at their...
Why Frameworks Are Lenses on a Security Program
When the second framework arrives, most teams make the same mistake.
The first one, usually SOC 2, took nine to twelve months and a large chunk of...
Operationalizing Security Policies: From PDF to Practice
The moment that usually exposes a security program is not the audit. It is a simple question asked in a meeting.
"Who actually reviews user access...
GRC Platform Managed Services: What You Actually Get
A company subscribes to a GRC platform. A consultant configures it, loads policies, maps controls, connects integrations. The dashboard turns green....
Compliance Consulting vs GRC Platform: You Need Both
The question surfaces early in most compliance conversations: do we need a consultant, or can we just use the platform?
It is a reasonable question....
CMMC Compliance Consulting for Canadian Defence Contractors
Canadian companies selling into the U.S. defence supply chain face a compliance requirement that is no longer theoretical. The Cybersecurity Maturity...
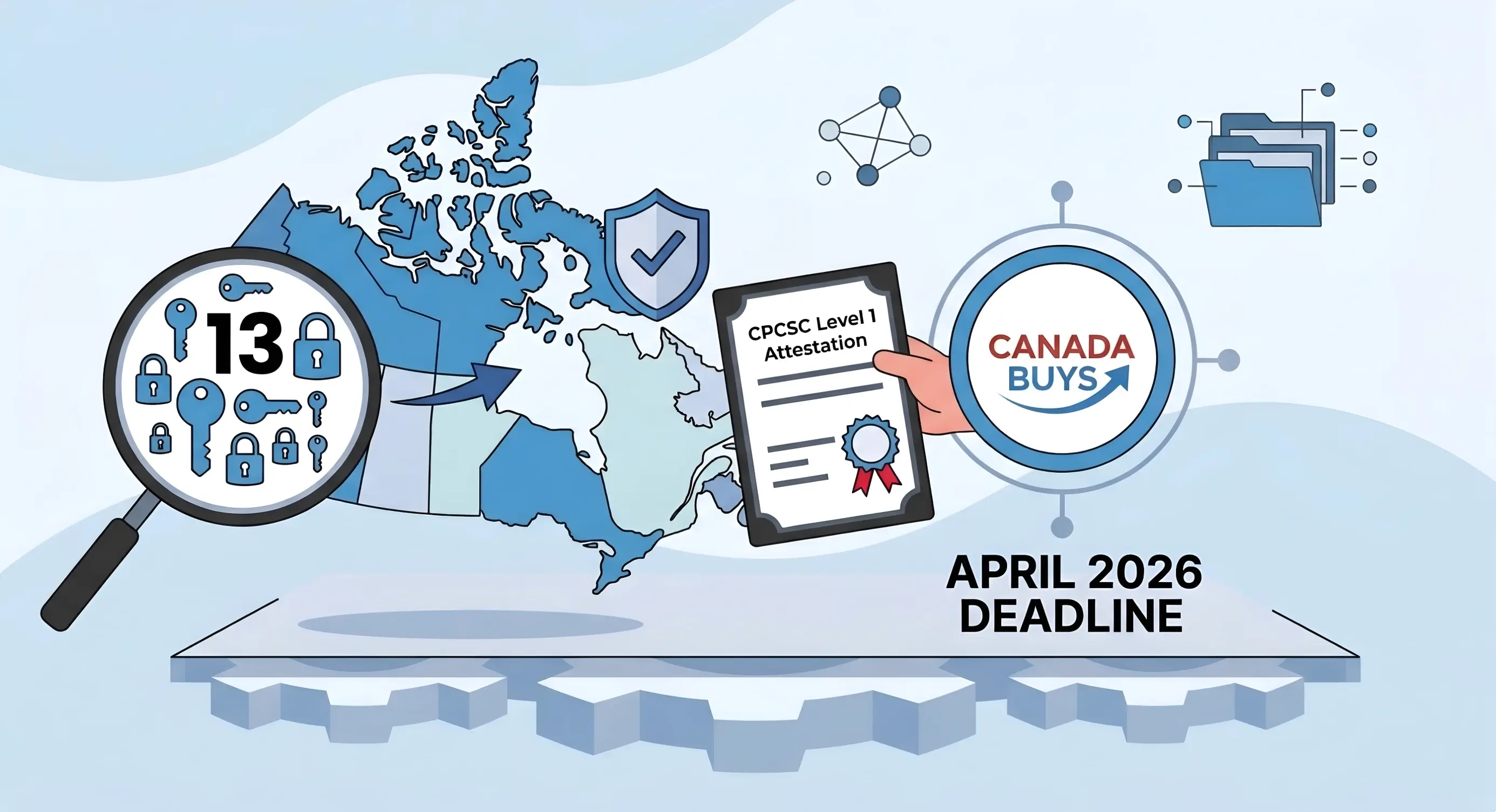
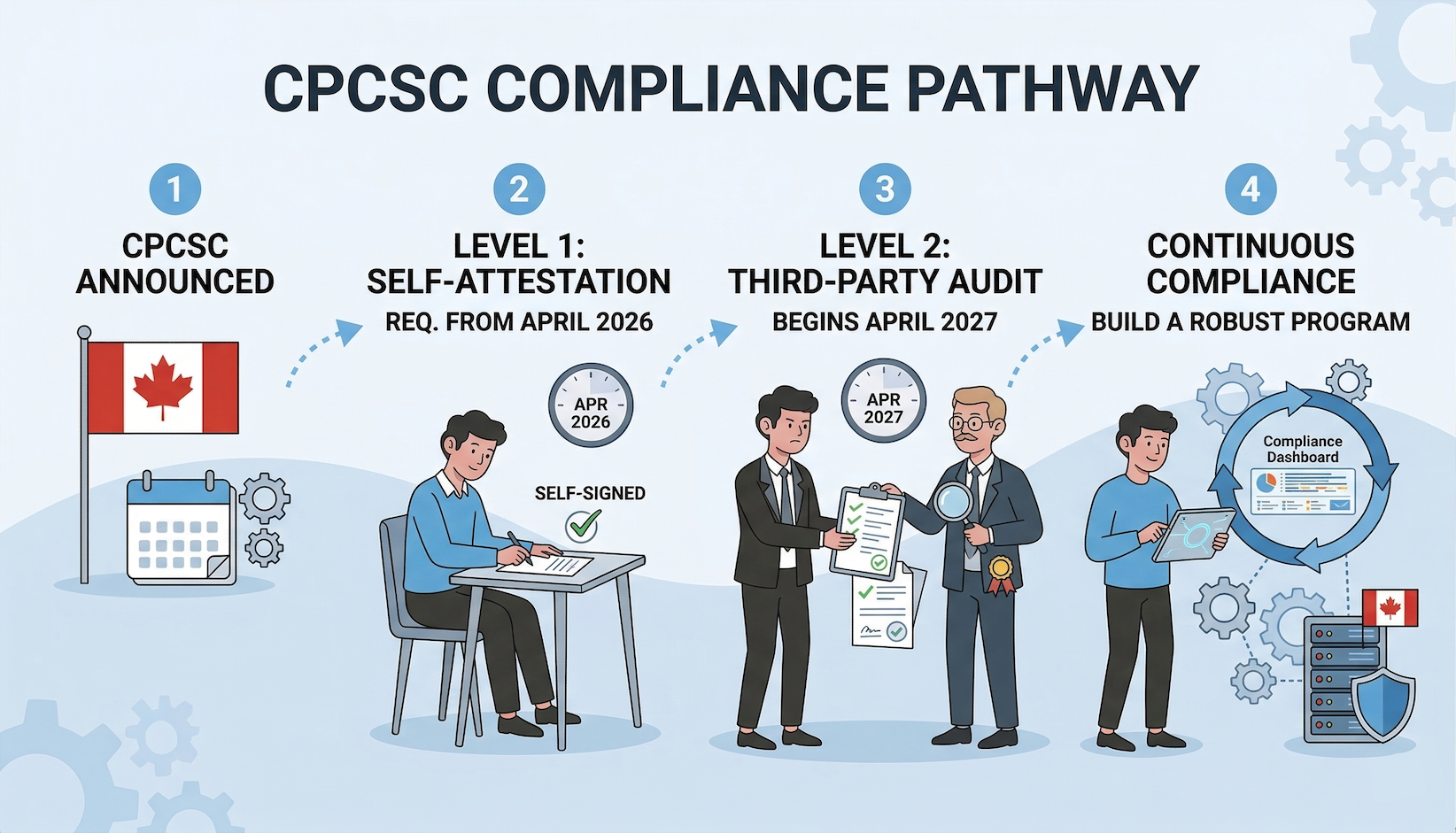
CPCSC Level 1 vs Level 2: The Cost Cliff Suppliers Miss
Canadian defence-adjacent suppliers keep running into the same pattern. A team clears CPCSC Level 1 in a few weeks, files self-attestation in Canada...
CPCSC Level 1 Scoping Before You Have a Contract
DND has been clear about direction and quiet about timing. Canada Buys is collecting expressions of interest, industry days are running, and the...
CPCSC Level 1 Self-Assessment: What Apr 14 Actually Requires
On April 14, 2026, the Government of Canada published the CPCSC Level 1 self-assessment guide, the scoping guide, and practical implementation steps....
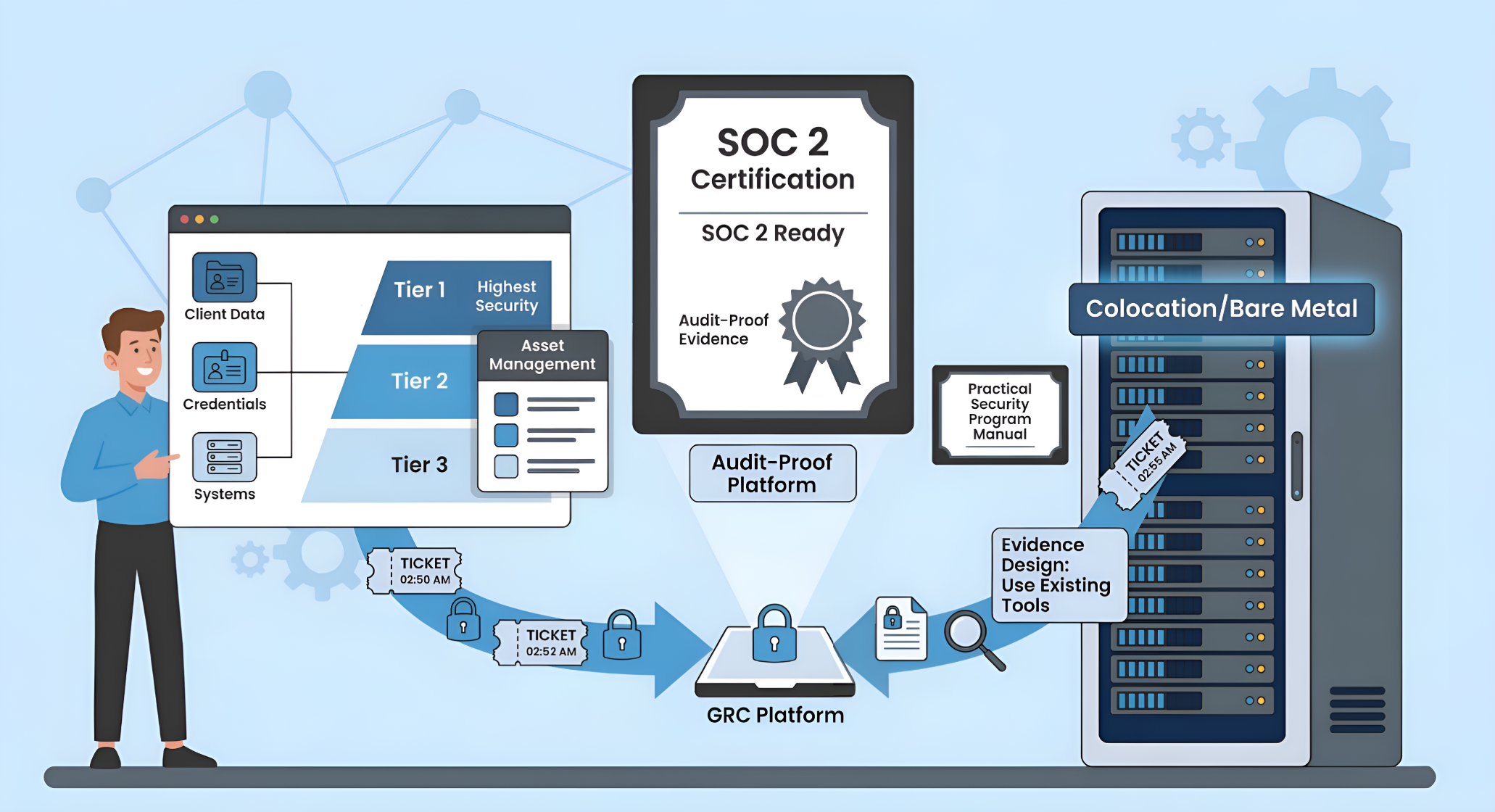
SOC 2 Vendor Management When Your Data Center Is a Subservice Organization
TL;DR
- When your data center is operated by another organization (a colocation or hosting provider), that organization is a subservice organization...
SOC 2 Change Management with Tickets Instead of CI/CD
TL;DR
- Change management maps to CC8.1, which has 14 Points of Focus covering authorization, design, testing, approval, deployment, segregation of...
SOC 2 Secure Development with Self-Hosted GitLab
TL;DR
- The same Trust Services Criterion that governs infrastructure changes governs code changes: CC8.1, change management
- Self-hosted GitLab is the...
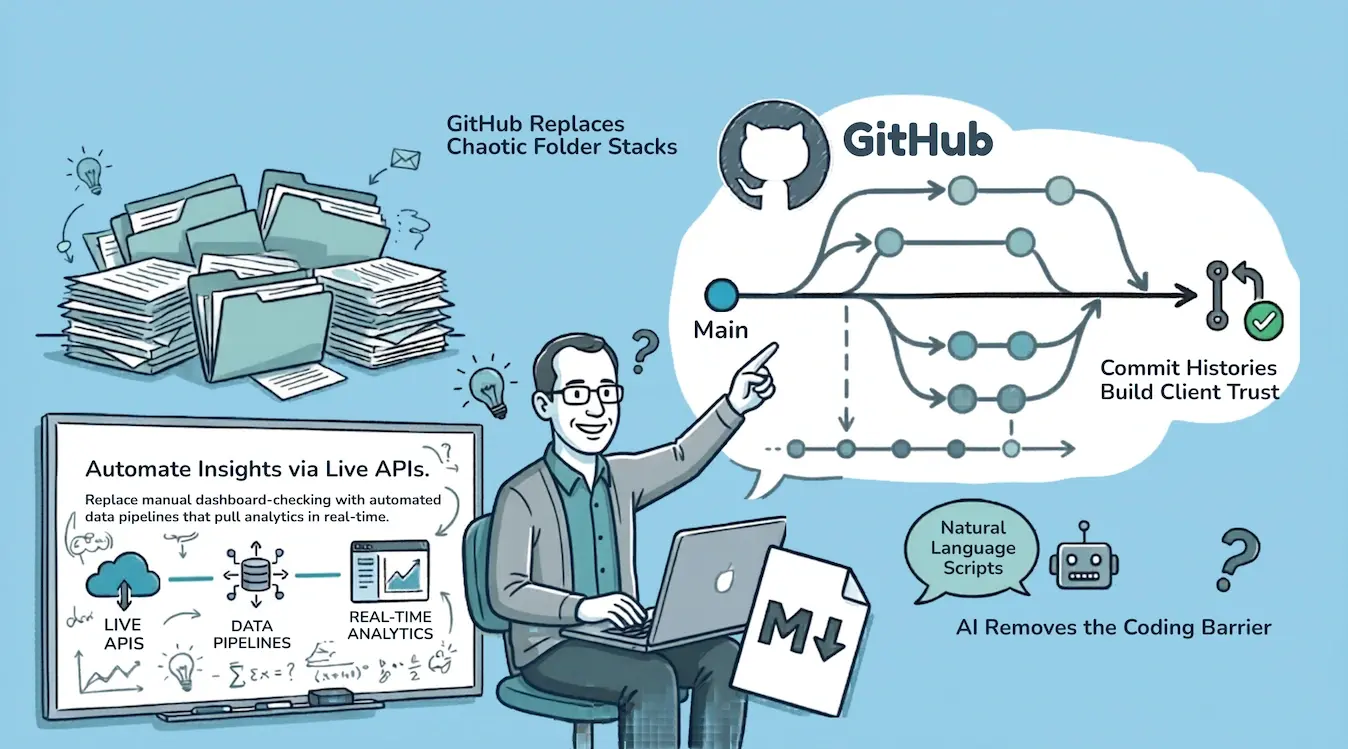
What Is Consulting as Code? How We Run a Cybersecurity Practice From GitHub
For years, programmers had an unfair advantage over the rest of us.
Not because they could build software. Because they could access data. Rich,...
The Real Cost of DIY Compliance vs. Hiring a Consultant
On paper, DIY compliance looks straightforward. Subscribe to a GRC platform, follow the control library, collect evidence, engage an auditor. The...
SOC 2 Consultants for On-Prem and Hybrid Infrastructure
Most SOC 2 consultants know AWS. Some know Azure and GCP. Very few know what to do when your stack includes a colocation facility, a bare-metal...
ISO 42001 Certification Cost: What You'll Actually Pay in 2026
If you are an AI SaaS company looking at ISO 42001, the first question is not what does the standard say. It is what is this going to cost us in...
SOC 2 in 90 Days: What That Timeline Actually Requires
Ninety days from kickoff to a SOC 2 readiness is achievable. It is not achievable for every company, and the companies that hit it make deliberate...
SOC 2 for Professional Services Firms: The Scoping Problem Nobody Warns You About
A professional services firm starts its SOC 2 process the same way most companies do. An enterprise client puts it in an RFP. The team subscribes to...
Fractional CISO for SaaS Companies: What the Role Actually Looks Like
Security leadership at most SaaS companies follows a predictable pattern. The CTO handles it. Not because they volunteered, but because nobody else...
CPCSC Compliance Consulting: What a Consultant Actually Does for Defence Contractors
CPCSC Level 1 attestation becomes a procurement requirement for Department of National Defence contracts in April 2026. Companies that can't attest...
What Does a SOC 2 Readiness Assessment Actually Include?
A SOC 2 readiness assessment is not the audit. It is the diagnostic step that tells a company exactly where it stands before committing budget and...
ISO 27001 Consultant in Canada: When It Makes Sense and What It Actually Takes
ISO 27001 certification gives you a one-to-two-page certificate. SOC 2 gives you a 40-to-50-page report describing every control, how it was tested,...
SOC 2 Implementation Cost and Timeline: What to Actually Budget
SOC 2 has four cost components. Most companies only budget for two of them, then get surprised by the rest halfway through the engagement.
Here is...
How to Choose a SOC 2 Consultant: A Checklist for SaaS Companies
The Two Types of SOC 2 Consultants
Platform-first firms compress the engagement into days or a few weeks. They take a policy template library, swap...
What Project Glasswing Actually Means for Your Security Program
I have been thinking about what Anthropic's Project Glasswing announcement actually means for the clients we advise. The honest answer is that it...
Risk Assessment and Security Planning for ITSP.10.171
The majority of ITSP.10.171 control families deal with operational security: how you configure systems, manage access, protect data. The Risk...
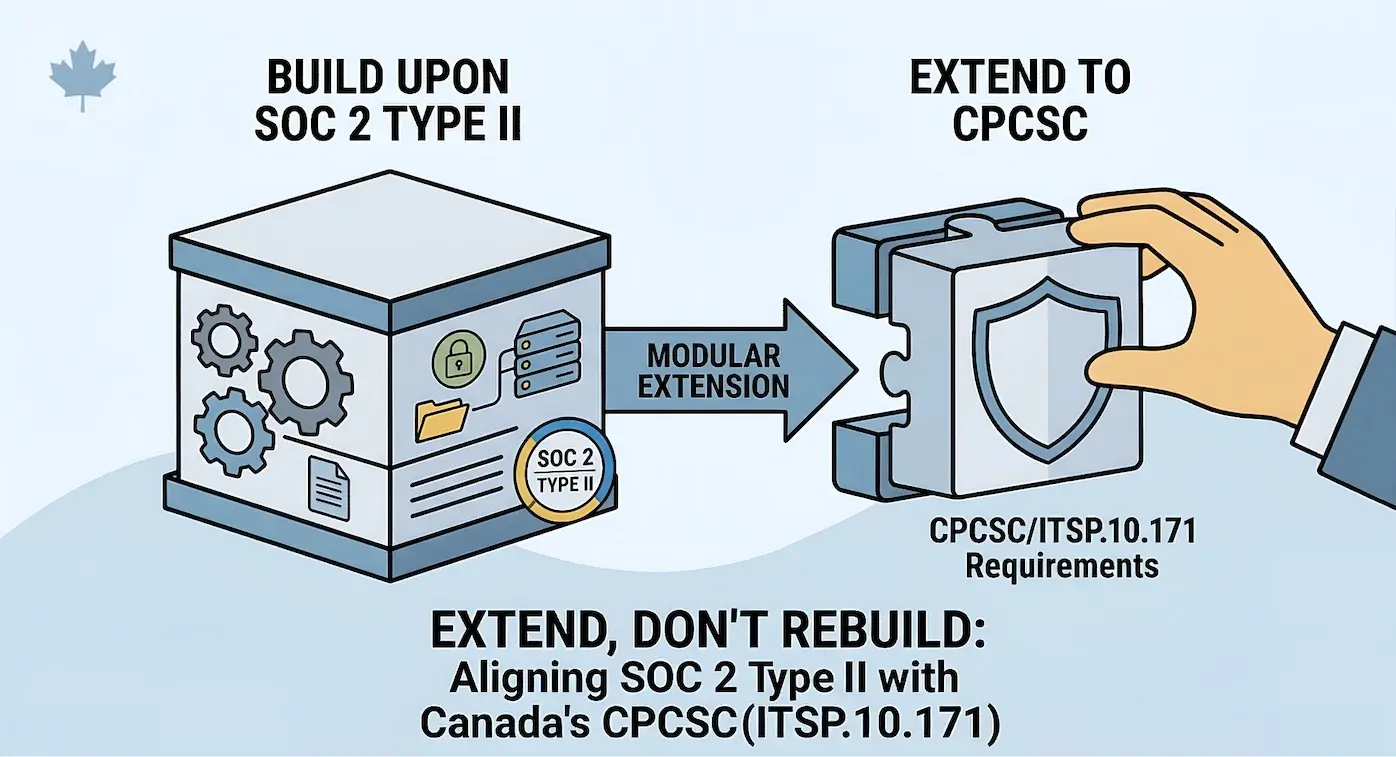
From SOC 2 to CPCSC: Extending Your Security Program for Defence Contracts
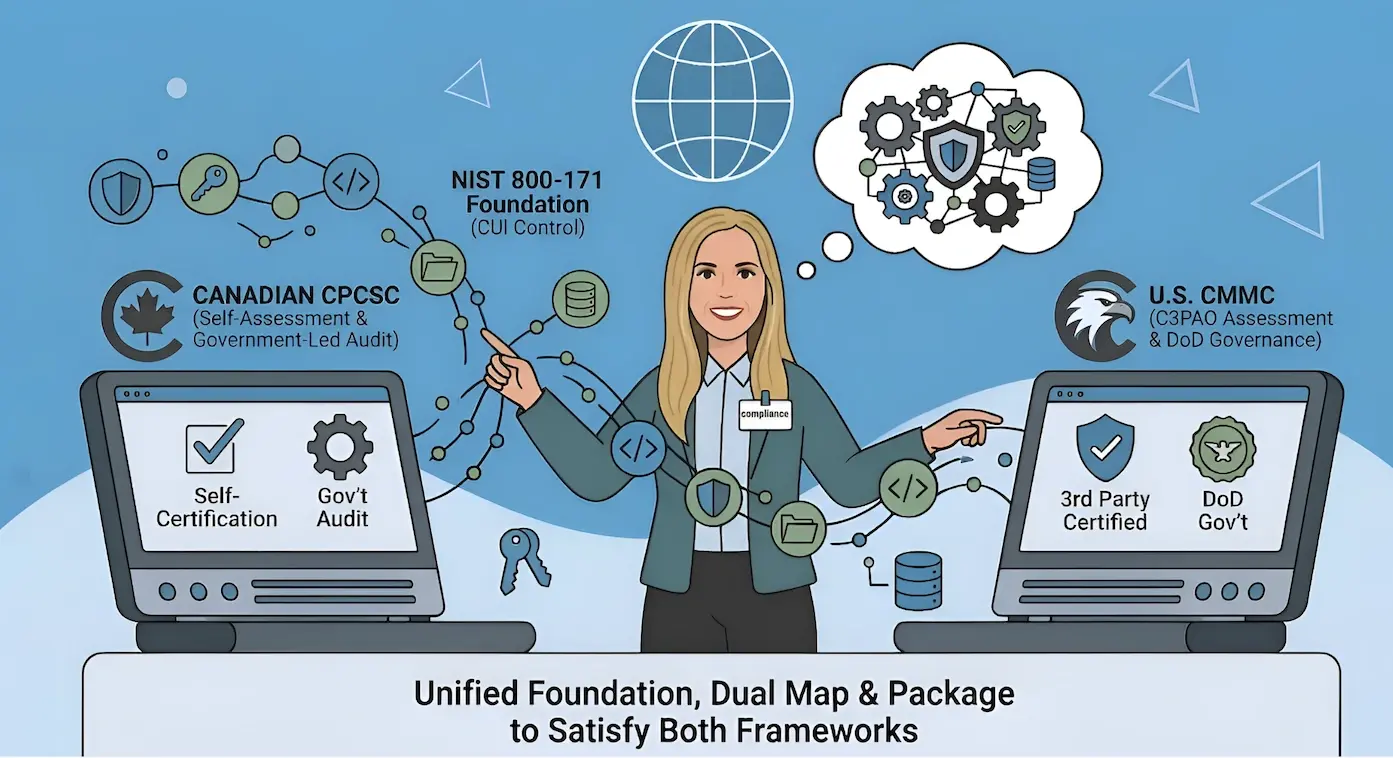
The question comes up consistently when companies with established security programs look at entering the Canadian defence supply chain: Do we need...
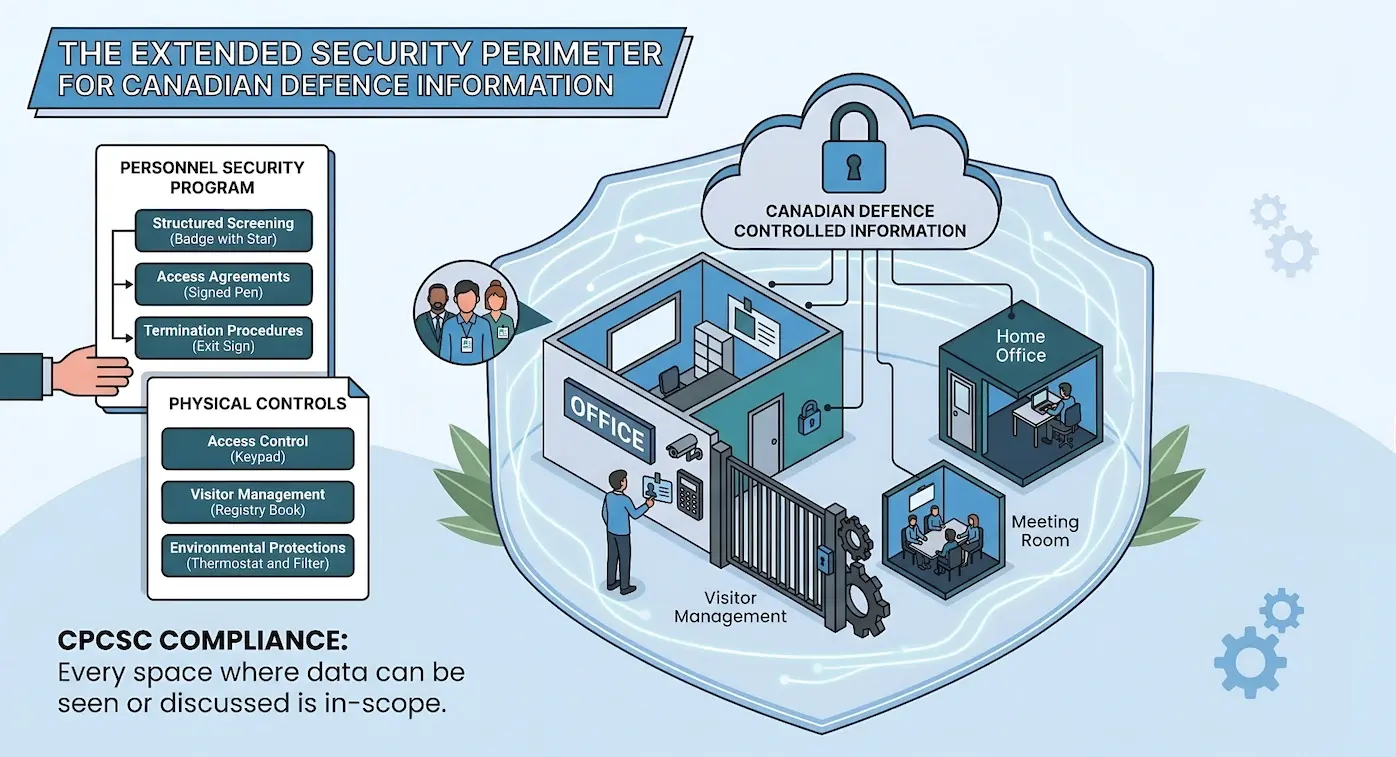
Physical Security and Personnel Controls Under CPCSC
Every other control family in ITSP.10.171 has a reasonable analogue in the commercial compliance world. Access control maps to SOC 2 CC6. Incident...
Protecting Controlled Information: Media and Communications Security (CPCSC)
In a compliance landscape that increasingly assumes cloud-first architecture, media protection controls tend to get deprioritized. The assumption is...
Incident Response and System Integrity Under CPCSC
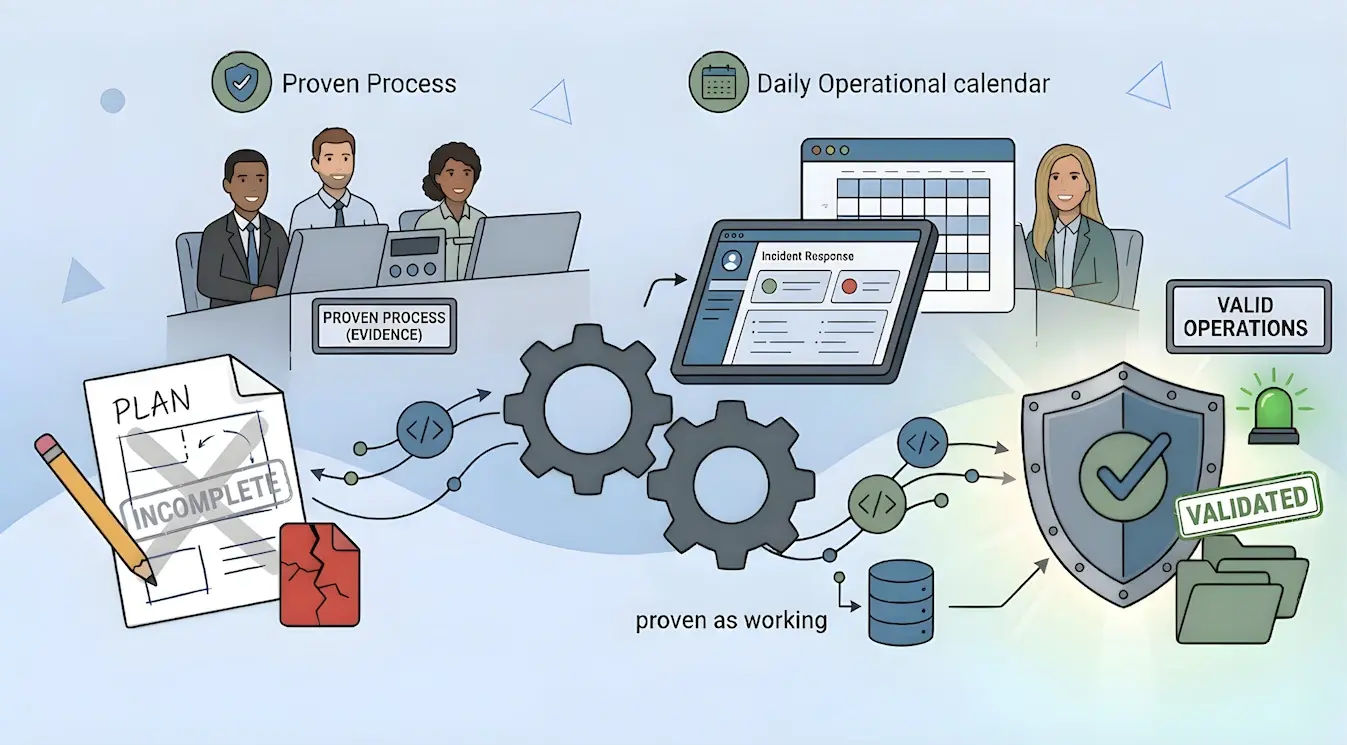
An incident response plan that exists only in a shared drive is not evidence of preparedness. It is evidence of intent, and the Canadian Program for...
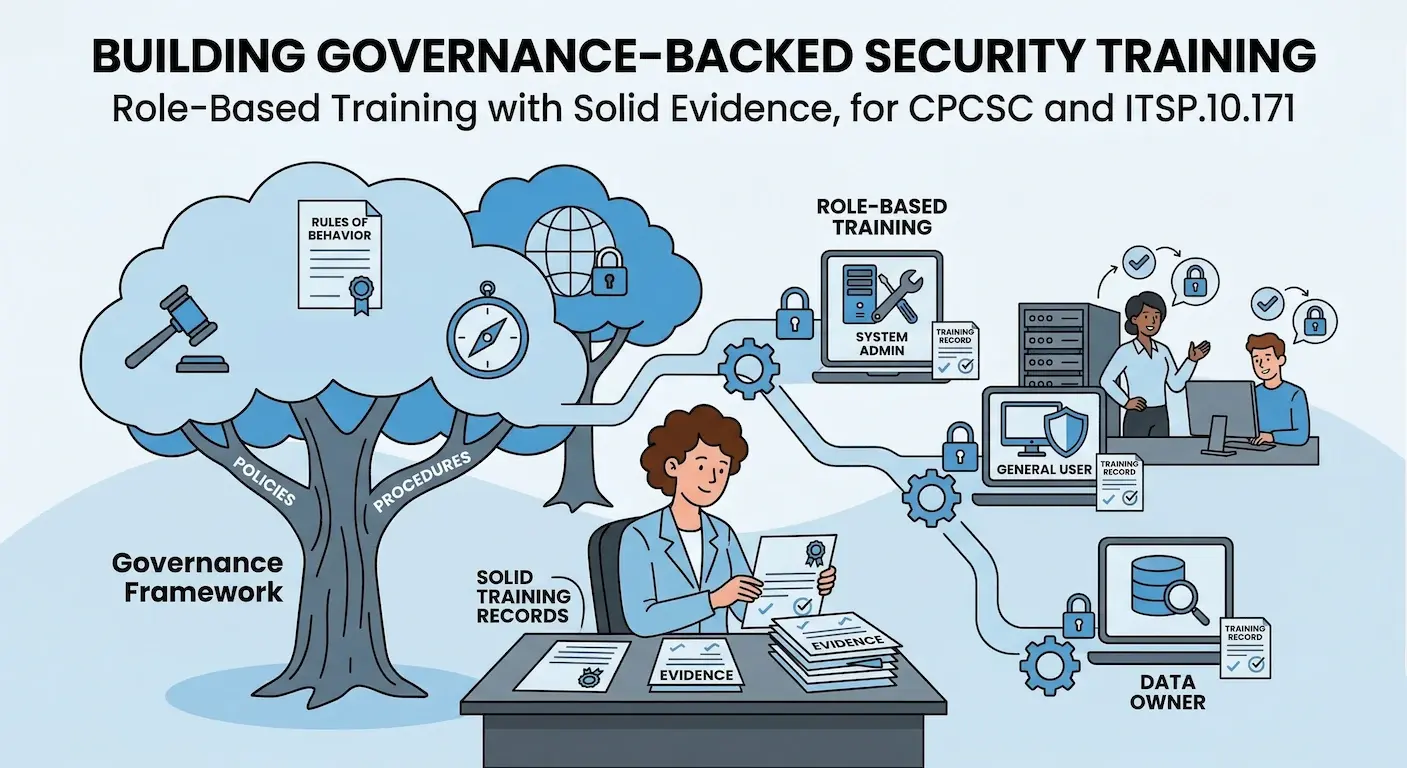
Security Awareness, Training, and Governance for CPCSC
The previous twelve posts in this series covered the technical and operational control families in ITSP.10.171: access control, incident response,...
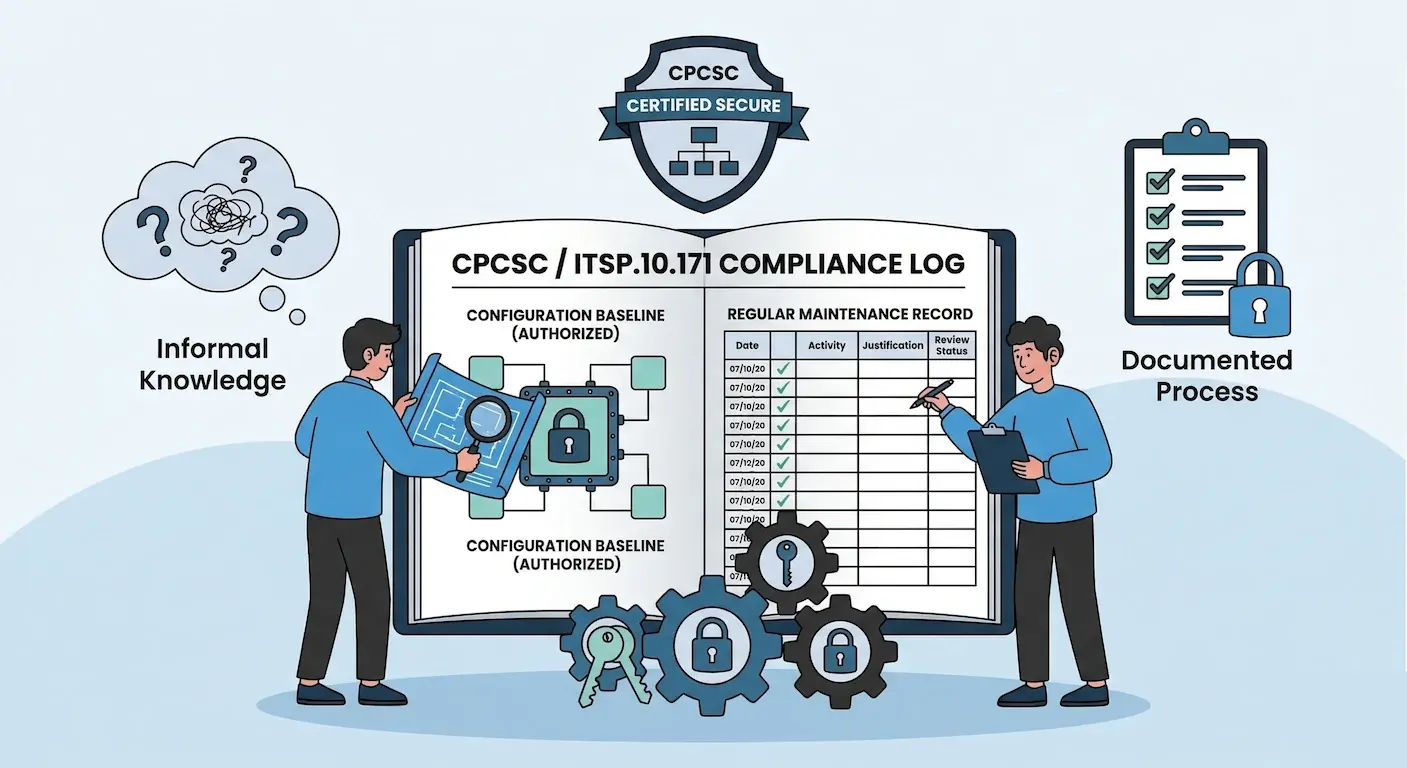
Configuration Management and System Maintenance for Defence Contractors
There is a specific phrase that comes up in nearly every environment that has never been through a formal configuration review: We know our systems....
Audit Logging, Monitoring, and Accountability for CPCSC
Most organizations produce logs. Application servers generate them, firewalls record them, identity providers track them. The volume is rarely the...
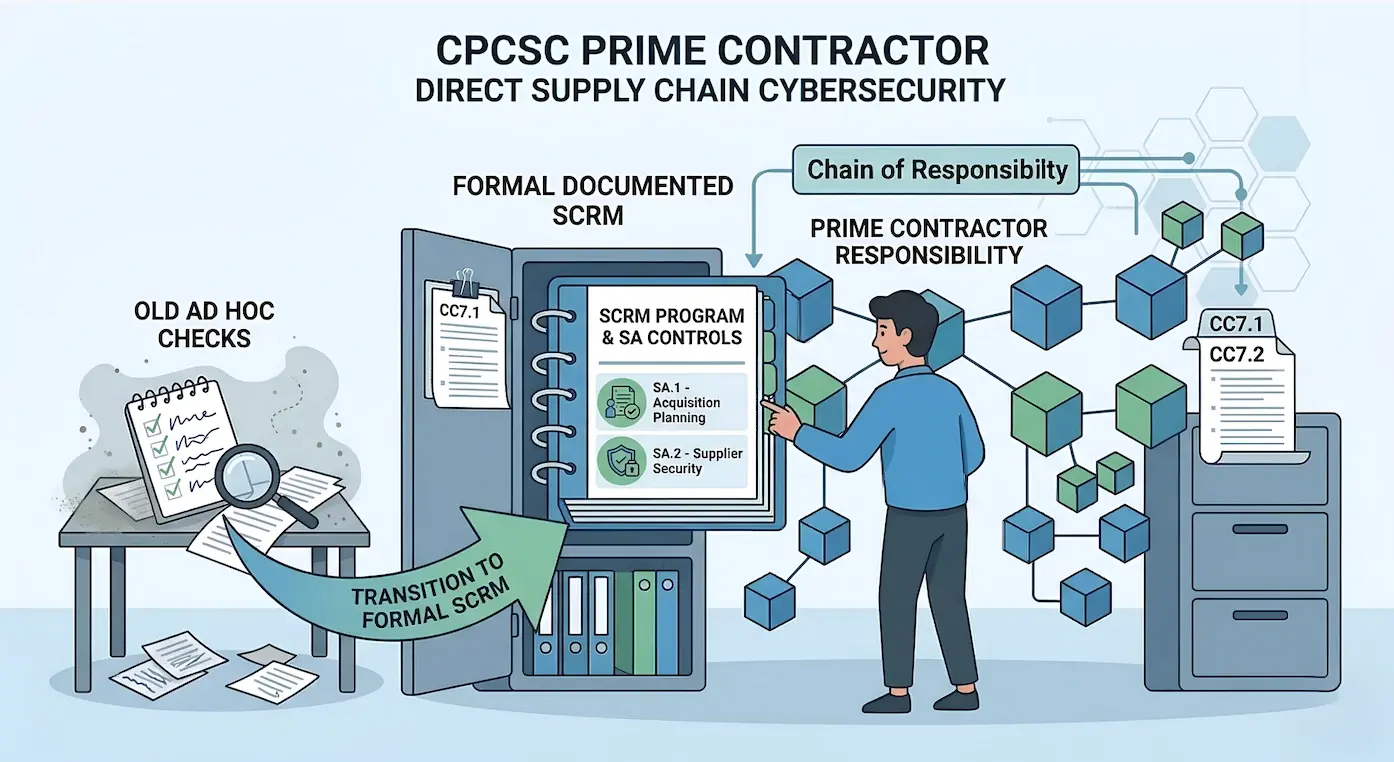
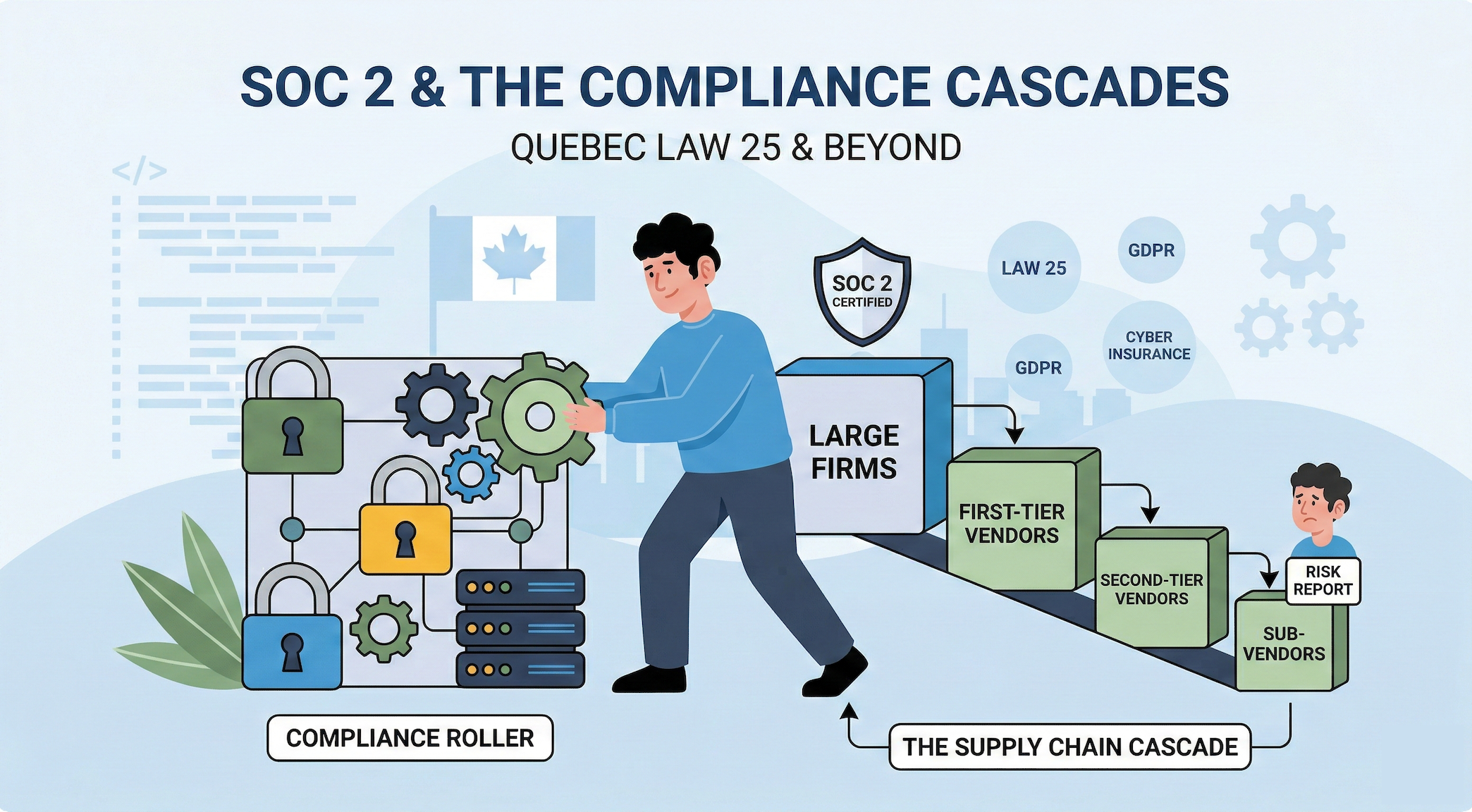
Supply Chain Risk Management Under CPCSC
For most of the history of Canadian defence procurement, cybersecurity obligations ended at the prime contractor's perimeter. A prime could hold a...
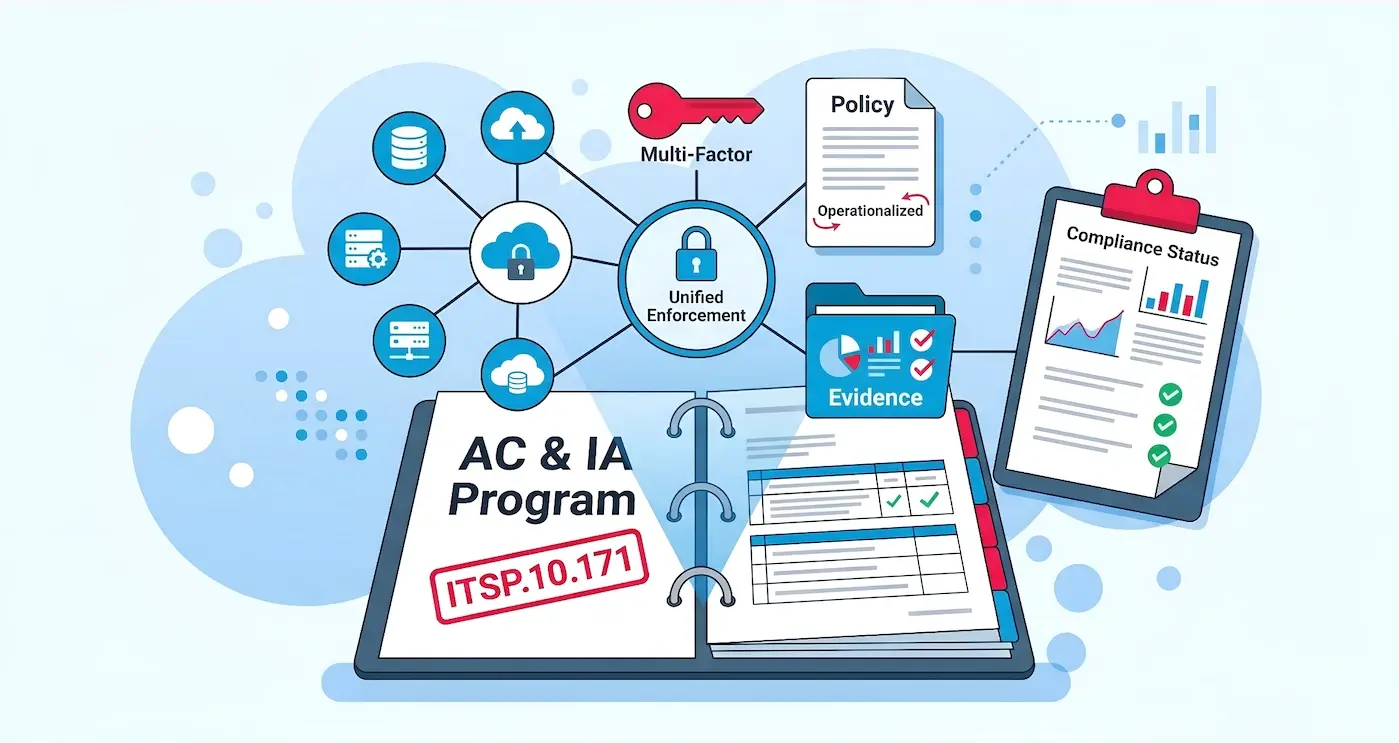
Access Control and Identity Management Under ITSP.10.171
Every security program has access controls of some kind. Password policies exist, MFA is probably enabled somewhere, and someone has a spreadsheet...
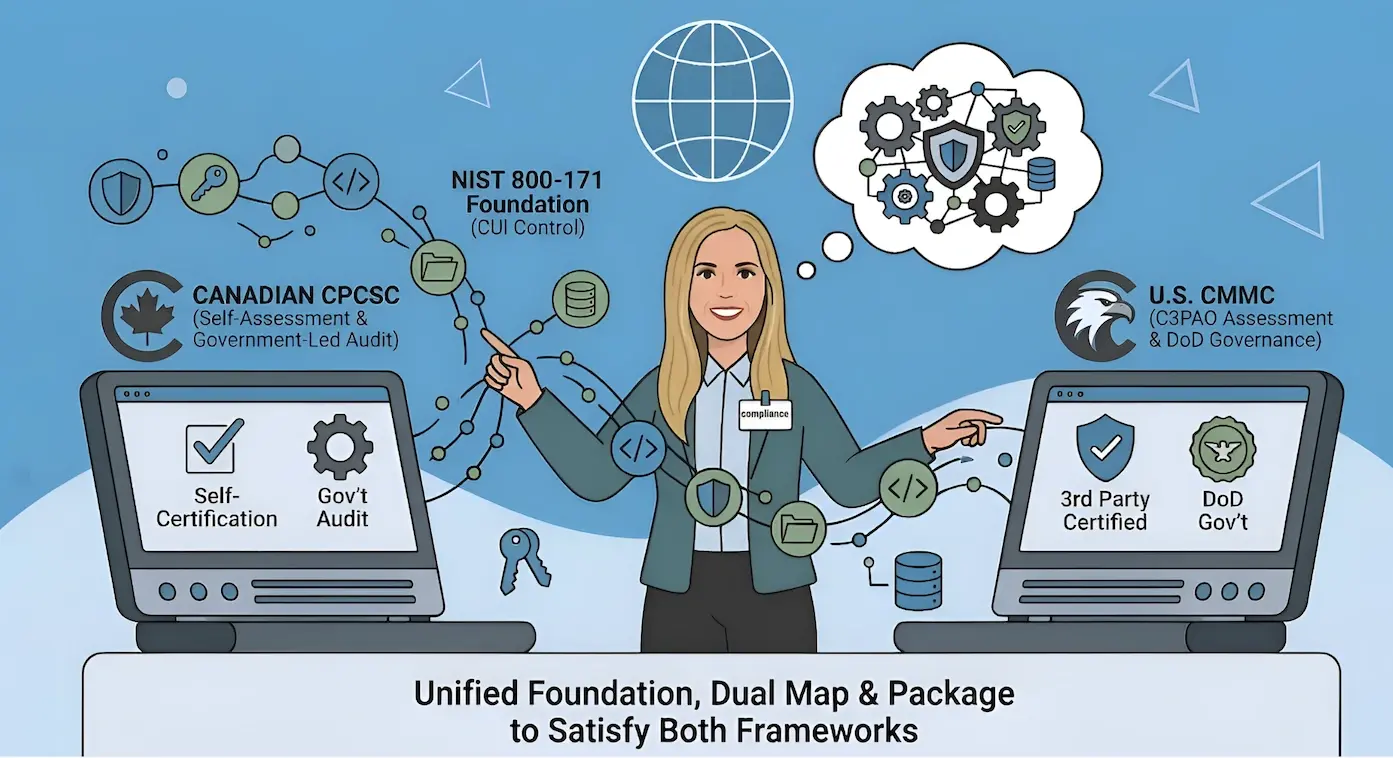
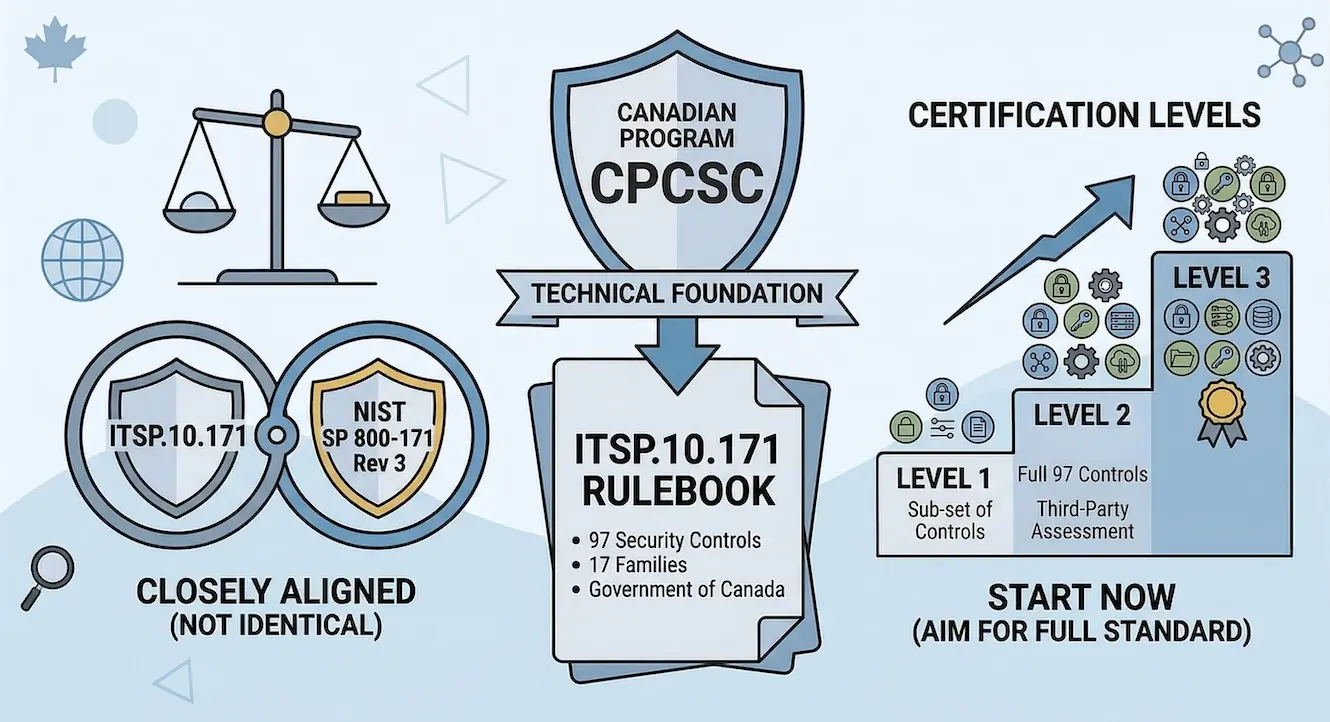
CPCSC vs CMMC: What Dual-Jurisdiction Contractors Need to Know
Companies operating in both the Canadian and U.S. defence supply chains face a question that does not have a simple answer: how do you satisfy two...
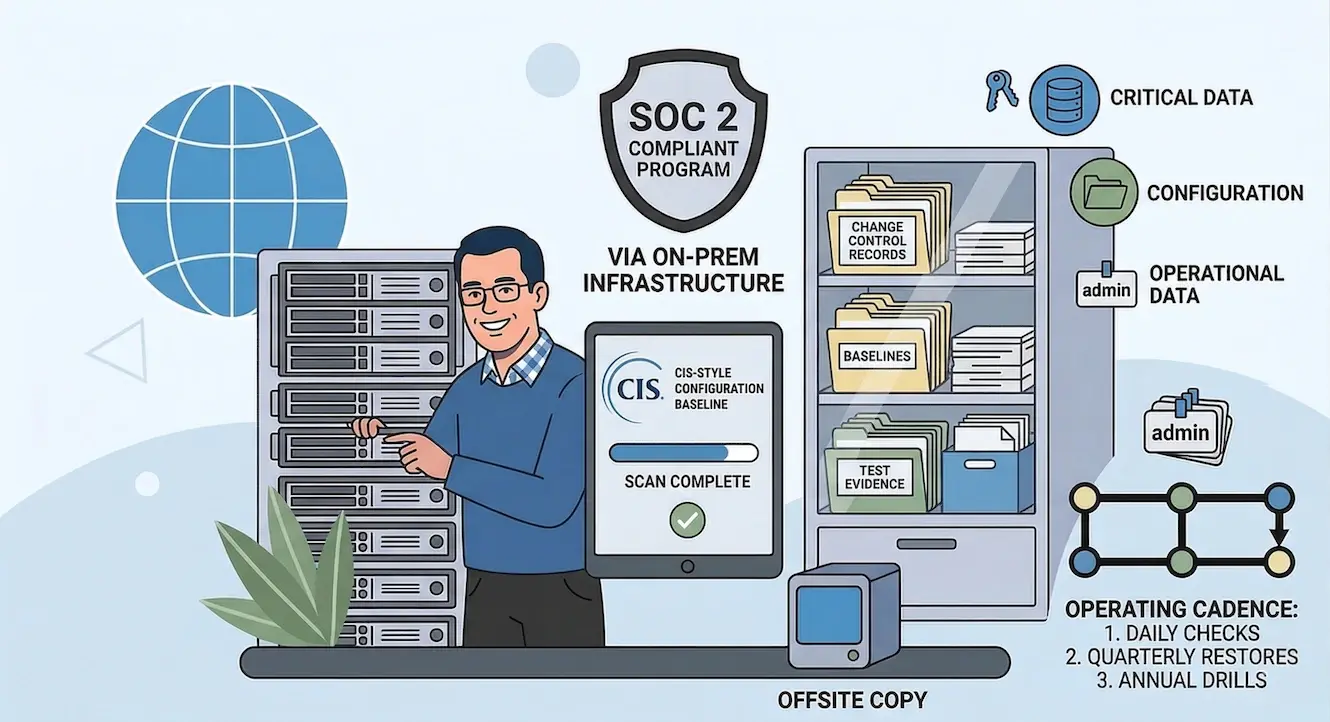
SOC 2 Configuration Baselines for Bare Metal: CIS Benchmarks & Beyond
In cloud environments, configuration compliance is a toggle. Enable AWS Config, deploy a conformance pack, and the platform continuously evaluates...
CPCSC Level 1 Self-Assessment: A Practical Guide
Level 1 self-assessment under the Canadian Program for Cyber Security Certification (CPCSC) is not a formality. Based on the program's alignment with...
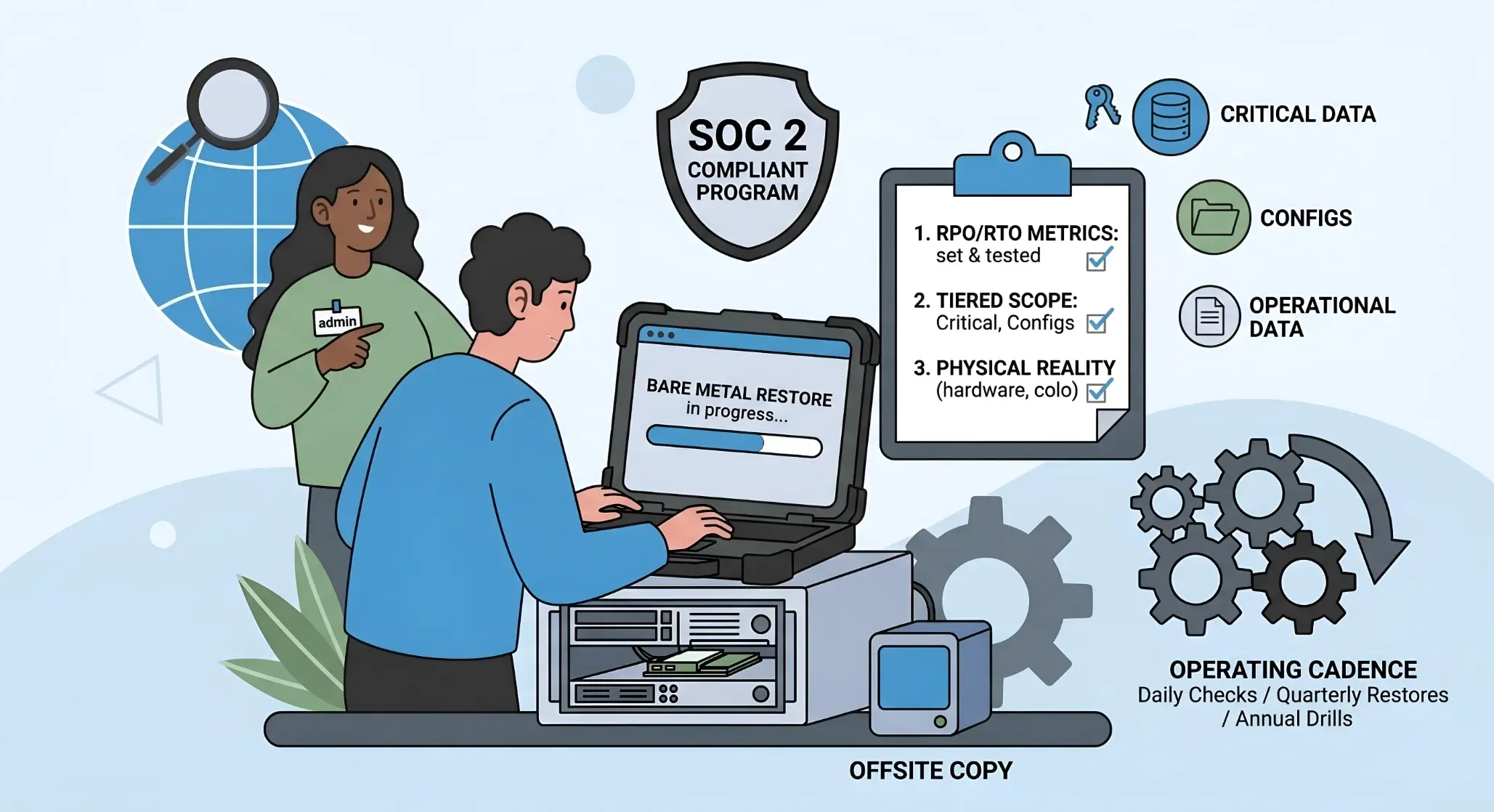
SOC 2 Backup and Disaster Recovery for On-Premise Infrastructure
Cloud disaster recovery is a region failover. Click a button, spin up infrastructure in another availability zone, and the platform handles...
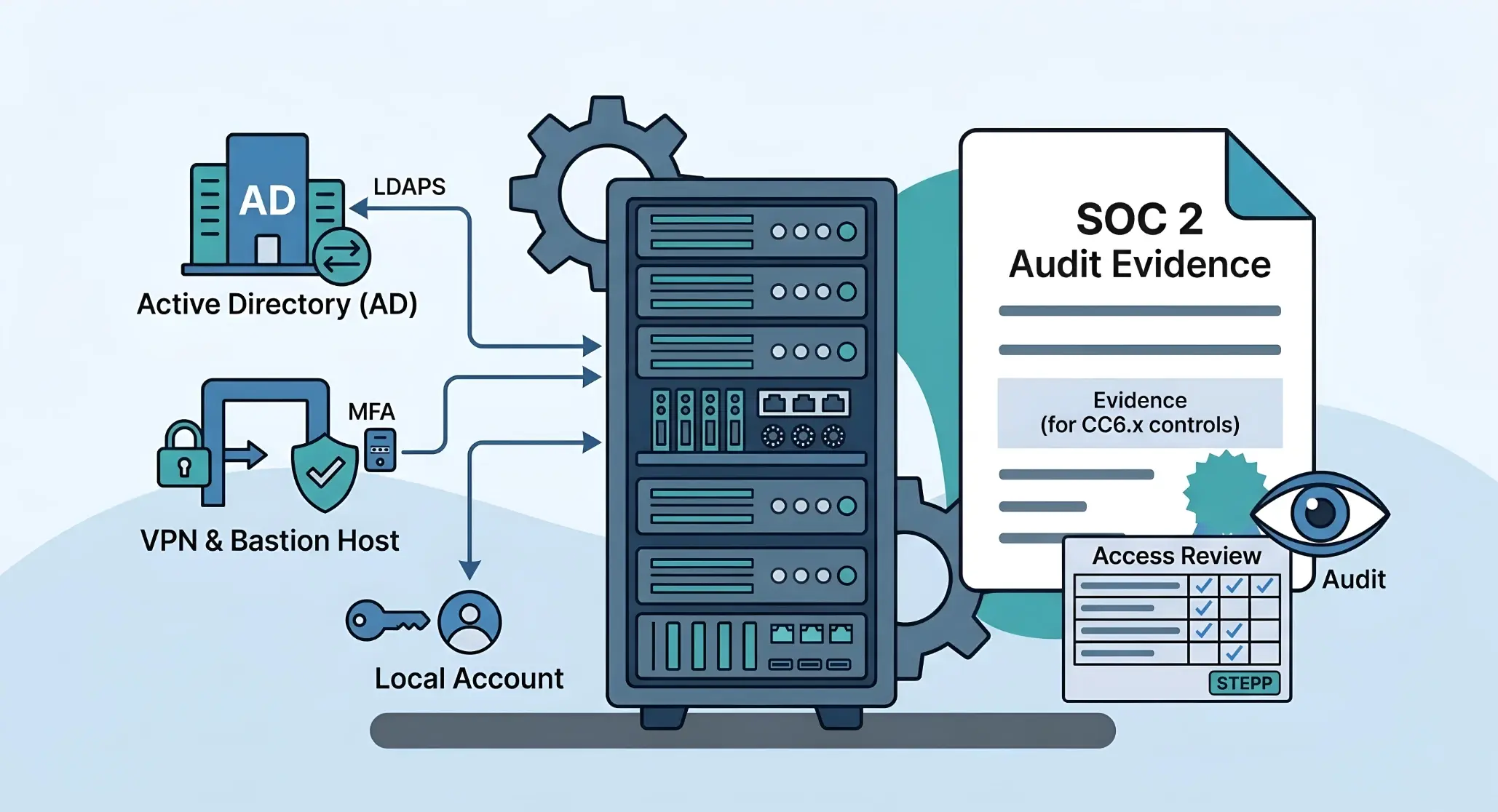
SOC 2 Access Control for On-Premise and Bare Metal Environments
In cloud environments, access control is a managed service. AWS IAM provides centralized identity, Okta handles SSO across every SaaS tool, and the...
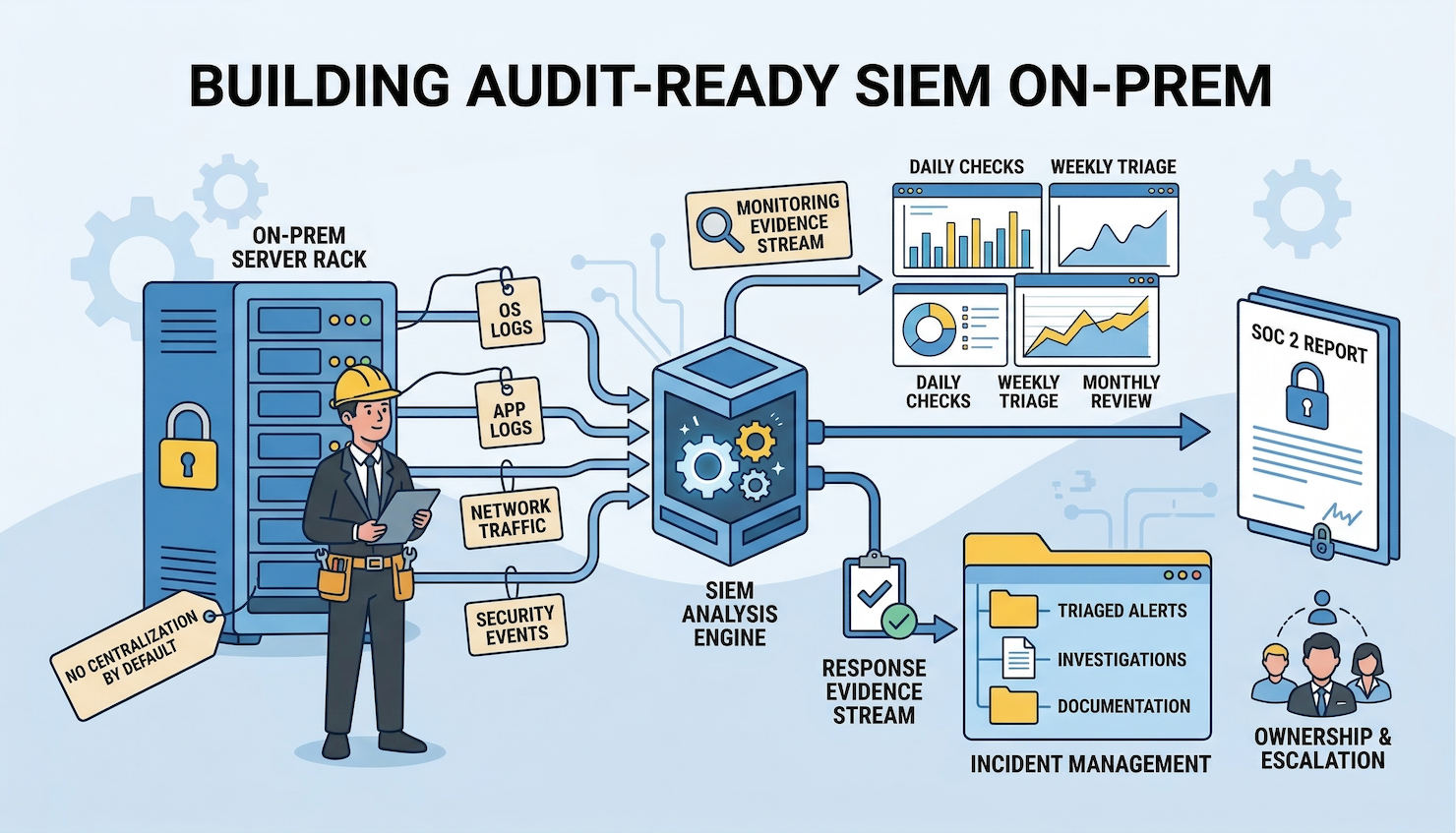
SOC 2 Logging and SIEM for Bare Metal Servers: Building the Evidence Layer
In a cloud environment, centralized logging is a toggle. Enable CloudTrail, turn on VPC Flow Logs, configure GuardDuty, and the compliance platform...
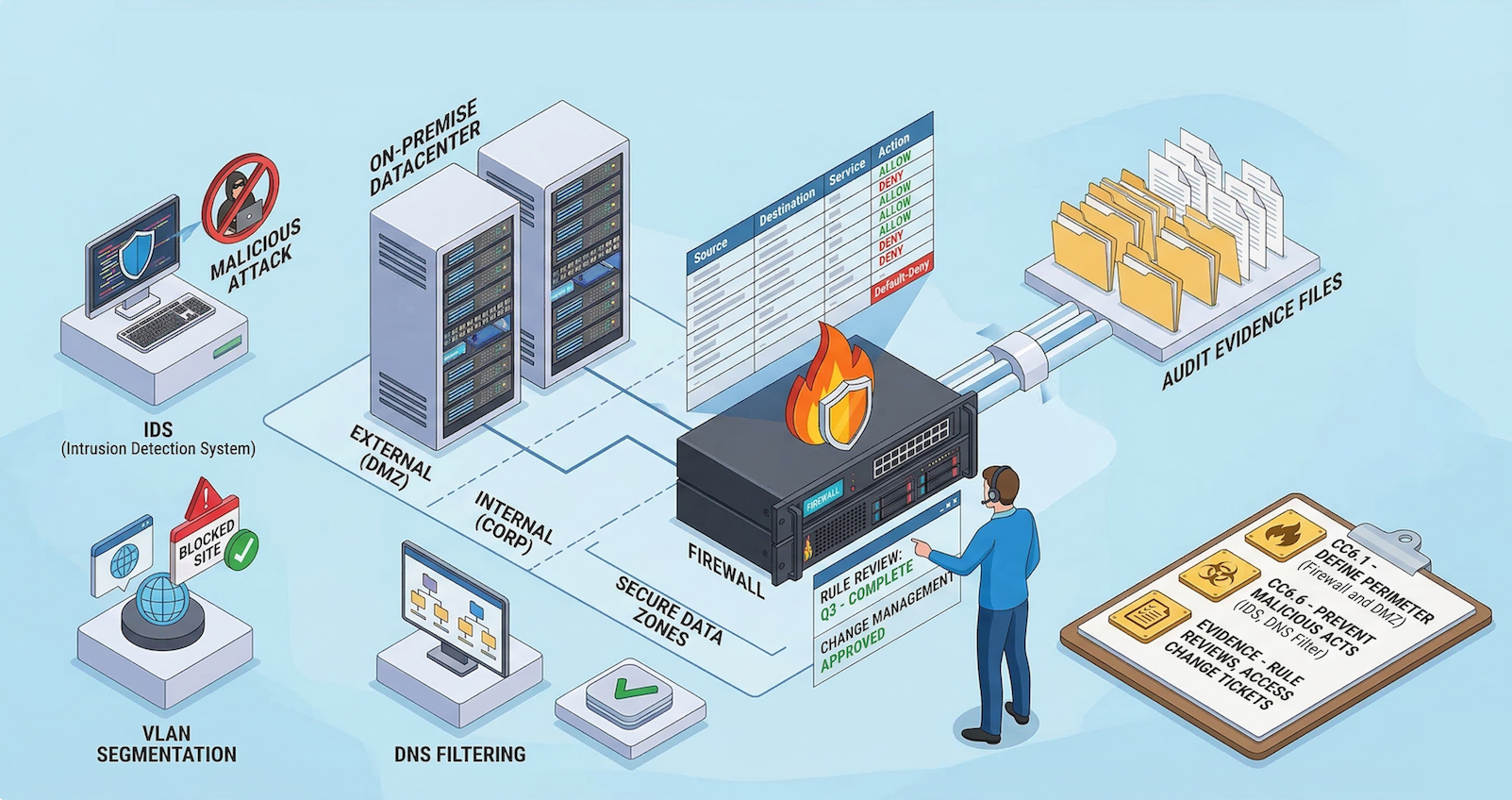
SOC 2 Network Security Controls for On-Premise Environments
Every SOC 2 guide on network security assumes the infrastructure lives in AWS. The advice is always the same: configure security groups, enable VPC...
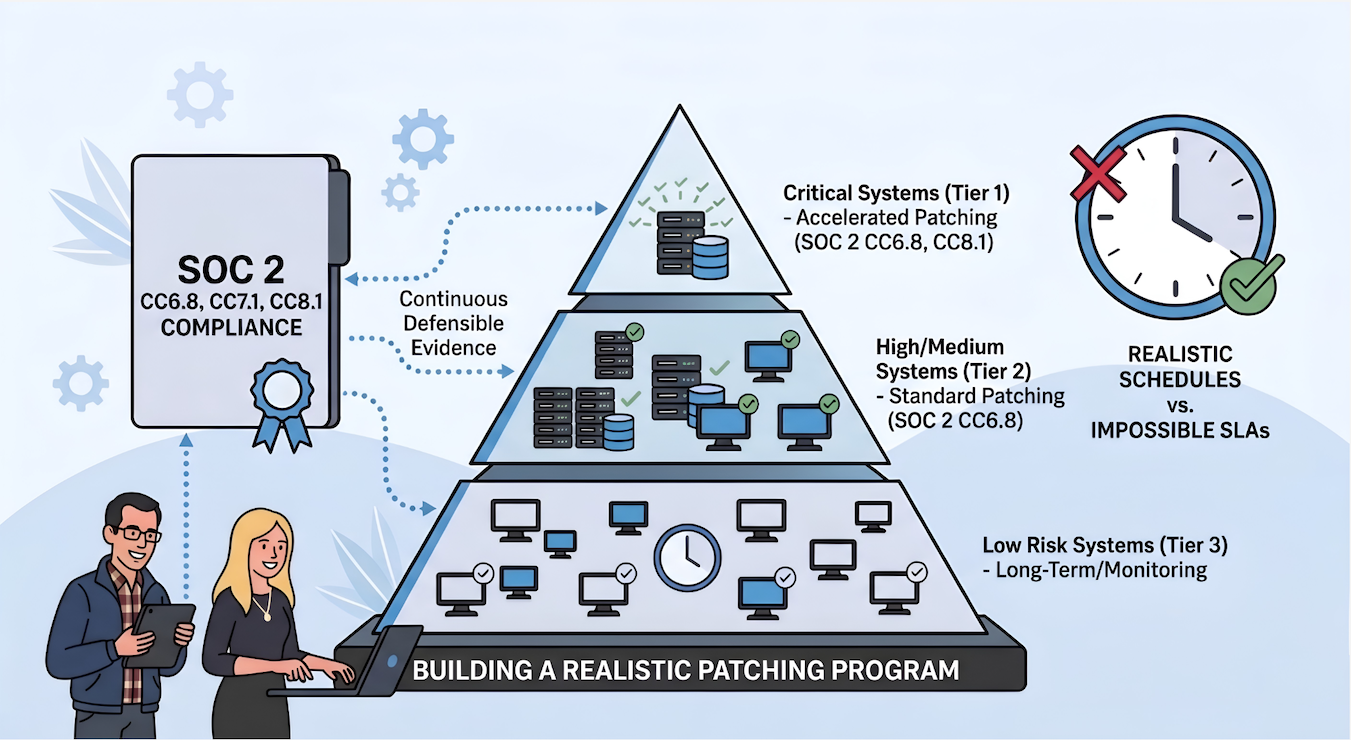
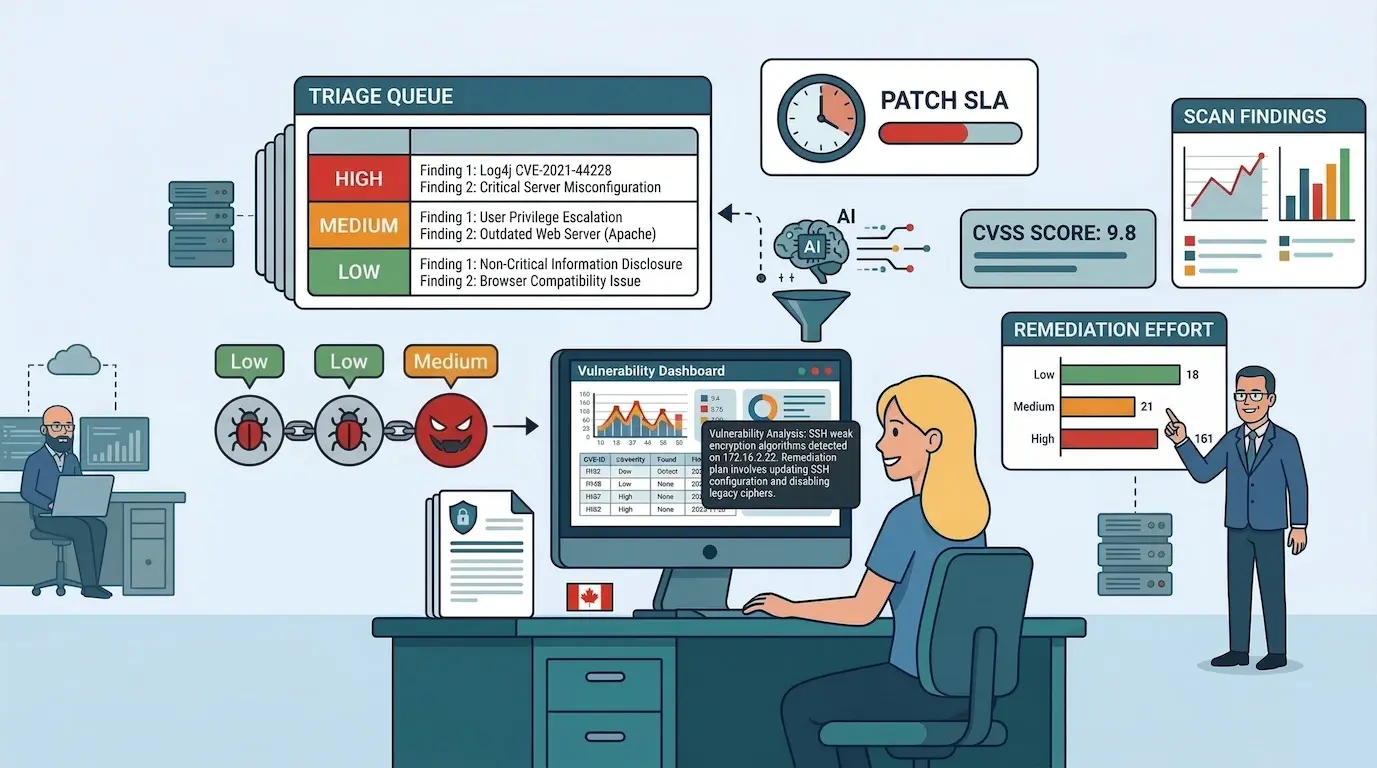
SOC 2 Vulnerability Scanning for On-Prem: Tiered Scanning Without Cloud-Native Tools
Every SOC 2 vulnerability scanning guide assumes the same starting point: connect a cloud-native scanner, enable automated assessments, and let the...
SOC 2 Readiness for Bare Metal SaaS: What to Expect When You Don't Run on AWS
A pattern keeps showing up. A SaaS company that has been running successfully for years, sometimes a decade or more, gets a call from a major...
The SOC 2 Snowball: How Law 25 Is Pushing Compliance Down the Supply Chain
SOC 2, and compliance in general, is self-perpetuating. Once a company achieves certification, one of the first things the framework requires is...
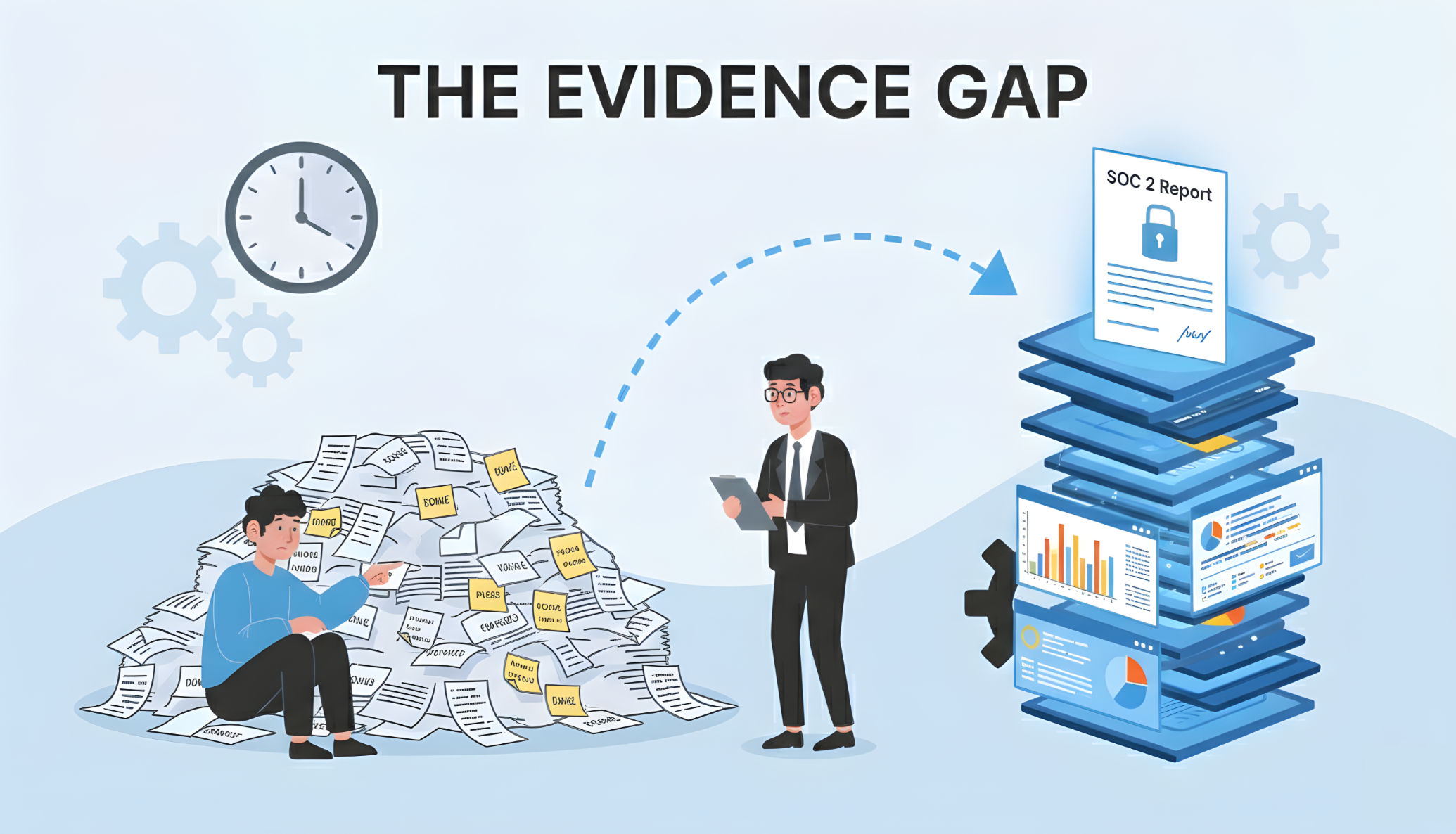
Bridging the Evidence Gap: How to Turn Solid Security into SOC 2 Compliance
The most common compliance gap has nothing to do with missing controls. It's missing evidence.
Across our engagements, the pattern is consistent:...
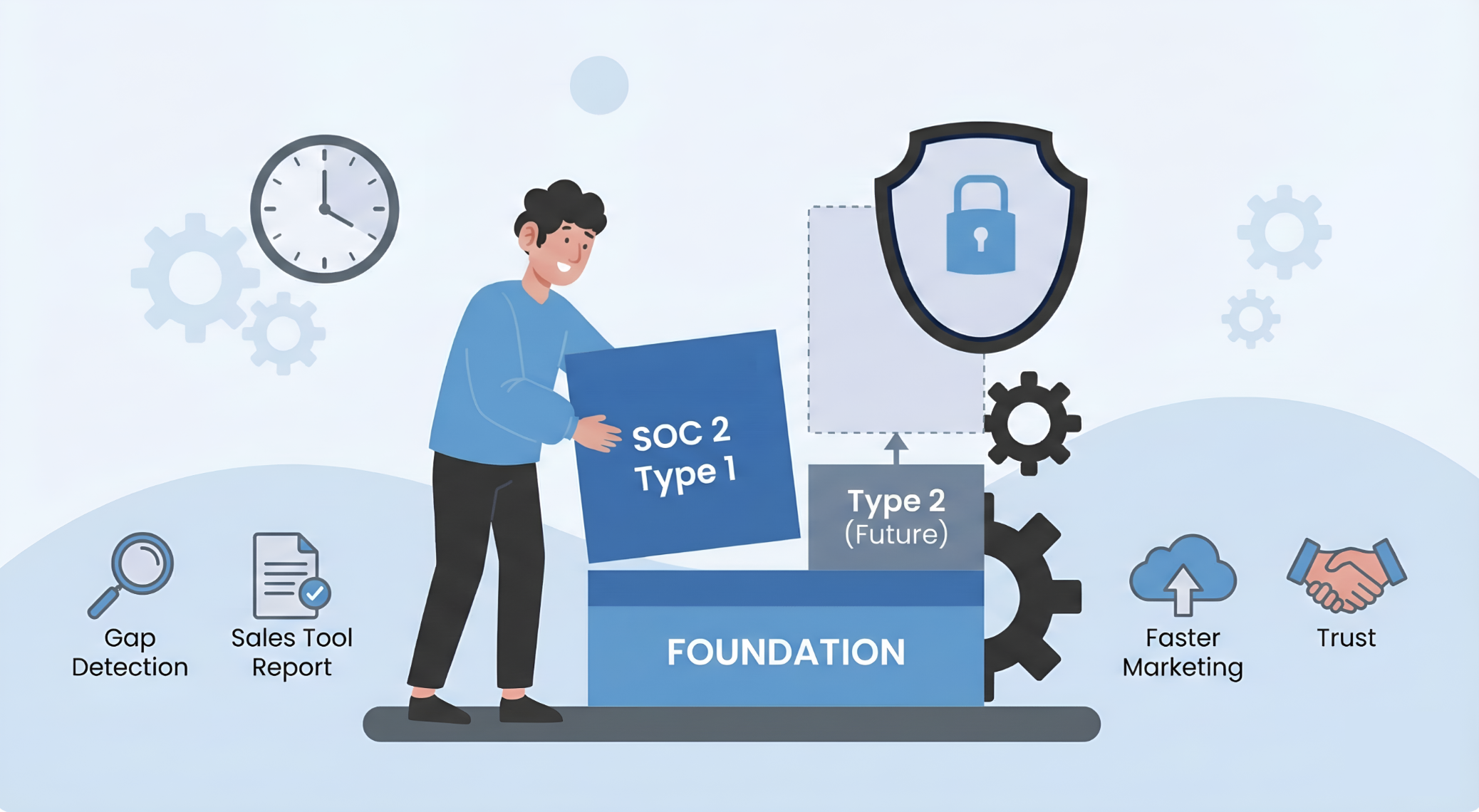
Why We Recommend SOC 2 Type 1 (Even Though You Don't Need It)
Most companies skip straight to Type 2. It's the *real* SOC 2, right? Type 1 is just not worth it. We used to think that way too. We've changed our...
SOC 2 Ticketing & SLAs: Vulnerability Patching & Incident Response
TL;DR: SOC 2 compliance requires a formal, trackable process for all security-relevant activities. Under the Trust Services Criteria, this means...
SOC 2 People Scoping: Which Employees, Contractors, and Vendors Are In Scope
TL;DR: The core question for SOC 2 people scoping: does their role or access affect your system's ability to meet its Trust Services Criteria...
Automate CI/CD Security for SOC 2: SAST, SCA, DAST Integration Guide
As a CTO, securing your CI/CD pipeline is critical for SOC 2 compliance. This guide shows you how to automate essential security scans, Container...
Supply Chain Cyber Risk: Why Your Vendors' Security Is Your Problem
Supply chain cyber risk has become one of the most pressing cybersecurity challenges for businesses of all sizes. A single compromise in a supplier’s...
Understanding ISO 42001: Why It Matters for AI Companies
In the ever-evolving world of artificial intelligence (AI) and software-as-a-service (SaaS) industries, staying ahead of regulatory and operational...
Why Invest in Compliance Automation If You Only Need SOC 2?
TL;DR: Even when SOC 2 is the only compliance requirement on the table, a compliance automation platform (Vanta, Drata, Secureframe, Scrut) pays for...
Security Questionnaire Automation: From Fire Drill to System
Security Questionnaire Automation: From Fire Drill to System
A 200-question security questionnaire lands in the sales team's inbox on a Thursday...
What Is Cyber Security Posture? Definition and Importance
Like in any industry, cyber security and cybercrime is constantly evolving. To keep up, you need to remain familiar with upcoming trends and the...
SOC 2 Trust Services Categories: Security, Availability, and Beyond
As a startup navigating the complexities of data security, understanding SOC 2 compliance is essential. SOC 2 (System and Organization Controls 2) is...
Shift-Left Cybersecurity Compliance: Benefits & Challenges
New business reality is that companies must prioritize cybersecurity compliance to protect customer data and demonstrate their security posture. The...
SOC 2 Renewal: What Changes the Second Time Around
For many SaaS companies, achieving SOC 2 compliance is a major milestone, a sign that they take security and customer trust seriously. But the real...
What Is a SOC 2 Type 2 Report and Why Does It Matter?
TL;DR: A SOC 2 Type 2 report is an independent audit that evaluates whether an organization's security controls are operating effectively over a...
How to Build a Security Program That Maps to Any Framework
Every compliance framework, SOC 2, ISO 27001, CMMC, HIPAA, asks the same fundamental question: does this organization have an effective security...
A Practical Guide for Ransomware Response
Ransomware attacks are among the most disruptive forms of cybercrime, locking businesses out of their own data and demanding ransom for its release....
GRC Engineering: What It Actually Takes to Build Compliance Into How You Operate
The term GRC engineering gets thrown around in conference talks and vendor marketing as if it's a single product you can install. It isn't. GRC...
SOC 2 Compliance Roadmap: From Gap Assessment to Audit-Ready
Every SOC 2 roadmap on the internet reads the same way: pick a platform, connect your integrations, run the gap analysis, remediate, audit. Five...
SOC 2 vs. ISO 27001: What Actually Overlaps, What Doesn't, and How to Decide
A question that comes up in nearly every initial engagement: Should we do SOC 2 or ISO 27001? Sometimes followed by Can we do both without doubling...
SOC 2 CSOCs Explained: Carve-Out vs Inclusive Method for Subservice Organizations
During a recent SOC 2 engagement, the question came up: the company runs its production systems in a colocation facility. Physical security, power,...
What Is ISO 42001? The AI Management Standard Explained
What Is ISO 42001? The AI Management Standard Explained
ISO/IEC 42001:2023 is the world's first international standard for managing artificial...
ISO 42001 and the EU AI Act: What Actually Maps and What Doesn't
The Compliance Question Every AI Company Is Asking
The EU AI Act entered into force on August 1, 2024, making it the first comprehensive AI...
ISO 42001 Software Costs: What to Budget for Certification
The Cost of AI Governance: Benchmarking Investment in ISO 42001 Compliance Software
Implementing ISO/IEC 42001 is a strategic necessity for AI SaaS...
AI-Specific Risks and Mitigation Strategies Under ISO 42001
AI-Specific Risks and ISO 42001: A Deep Dive for MLOps and Security Teams
For AI-driven SaaS companies, compliance with ISO/IEC 42001 is...
SOC 2 Automation with Vanta, Drata, and Others: What the Platform Won't Do for You
Six months after buying Drata, Vanta, Secureframe, or any other compliance automation platform, a company realizes the dashboard is half-populated,...
Security Logging and Monitoring Architecture for SOC 2 and ISO 27001
In cybersecurity, what you don’t know can hurt you. An unmonitored system is a black box where attackers can operate undetected for weeks or months. ...
Web Summit Vancouver: Gary Marcus on AI Limitations and Risks
Key Takeaways from the Web Summit Keynote: A Reality Check on the AI Hype
AI dominated the conversation at this 2025's Web Summit, and for good...
Using NRC IRAP Funding for SOC 2 and Cybersecurity Compliance in Canada
Most Canadian companies approaching compliance for the first time treat it as a cost. SOC 2 audits, gap assessments, penetration testing, GRC...
CMMC Level 1 Compliance: What the 15 Practices Actually Require
As of November 2025, CMMC is no longer a concept the DoD is considering. It is a contract requirement. Contracting officers are now including CMMC...
SOC 2 Compliance Automation: What Platforms Do and Don't Cover
Achieving SOC 2 compliance is a major milestone for SaaS companies and service providers handling sensitive customer data. Yet, for many startups and...
How to Implement ISO 42001: A Practical Guide for AI SaaS Companies
ISO 42001 is the first international standard for AI management systems, and most of the content about it reads like it was written by the standards...
ISO 42001 vs ISO 27001: What's Different and When You Need Both
Two Standards, One Security Foundation
ISO 27001 and ISO 42001 address fundamentally different risks, but they share more infrastructure than most...
ISO 27001 and SOC 2: How They Work Together (and Where They Don't)
A company finishes its first SOC 2 Type 2 audit, feels good about the result, and then gets a request from an international prospect asking for ISO...
SOC 2+ Audits: When Combining Compliance Frameworks Saves Time (and When It Doesn't)
A company that just finished its first SOC 2 Type 2 gets a new requirement from a customer in healthcare: they need evidence of HIPAA compliance. A...
AI Governance in GRC: How ISO 42001 Fits Into Your Compliance Program
As artificial intelligence (AI) rapidly embeds itself into core business processes, from customer support to code generation, enterprises face a...
ISO 42001 Compliance Software: 2026 Platform Review
The Platforms Compared
Vanta, Drata, Secureframe, and Scrut have all added dedicated ISO 42001 framework support. All four automate evidence...
Drata vs Vanta for ISO 42001 (2026 Comparison)
How They Compare
Both Drata and Vanta offer dedicated ISO 42001 framework support with automated evidence collection, control cross-mapping to ISO...
SOC 2 Trust Services Criteria: The Complete CC1-CC9 Reference Guide
If you are preparing for a SOC 2 audit and trying to understand what CC1.1, CC1.4, or CC6.2 actually mean, you are not alone. The AICPA's Trust...