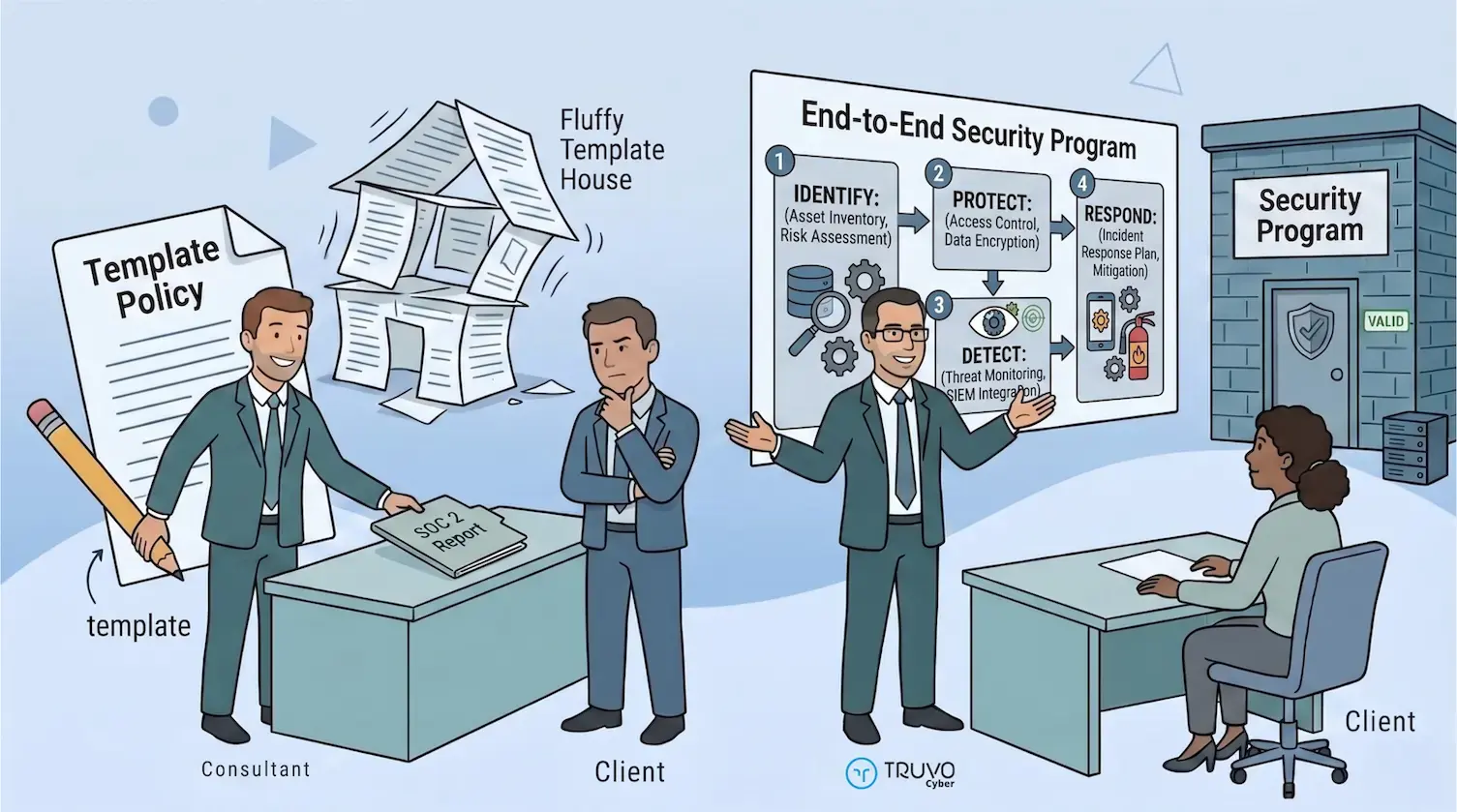
The Two Types of SOC 2 Consultants
Platform-first firms compress the engagement into days or a few weeks. They take a policy template library, swap in the company name, send documents for signature, configure a GRC platform with default controls, and hand the package to an auditor. Price can be under $15,000 for the full stack (GRC platform, audit prep, audit itself) on a 12-month contract. That should raise a flag.
This is not a security program. Nobody on the team actually reads the policies. Nobody understands what controls were selected or why. The first time a sophisticated buyer asks a question that goes beyond do you have a SOC 2 report, the gap becomes visible.
Program-first firms start with the company's actual architecture, team structure, and risk profile. The engagement takes 8 to 12 weeks. Policies are written for the specific organization. Controls are designed around how the team already works. The output is a security program that produces a SOC 2 report as a byproduct. If you are weighing whether to handle compliance internally or bring in outside help, that distinction is the crux of it.
The core difference
Both types get you the report. Only one gets you a program that holds up under scrutiny and runs after the consultant leaves.
The Evaluation Checklist
1. Do they start with scoping or with a platform demo?
A consultant who leads with a GRC platform demo is selling you the tool. A consultant who leads with questions about your architecture, team, and customer requirements is selling you the program.
Scoping determines which systems, people, data, and vendors are in scope. Get it wrong and you are over-scoped (paying to audit systems that do not matter) or under-scoped (producing a report that does not cover what customers care about).
Ask
Walk me through how you determine the scope of our SOC 2 engagement. If the answer skips straight to platform configuration, that is a signal.
2. Do they customize policies or use templates?
Template policies are easy to spot after the fact. Engineering reads them and says we don't do any of this. Access review procedures reference tools the company does not use. Change management policies describe a process nobody follows. The policies exist for the auditor, not for the team, and the program decays the day the engagement ends.
Ask
Can you show me a sample policy and walk me through how you would customize it for our stack? If they cannot explain how the policy adapts to your architecture, deployment pipeline, or team structure, the customization is cosmetic.
3. Do they understand your infrastructure model?
A consultant whose practice is built around SaaS on AWS will struggle with bare metal, colocation, or hybrid cloud. The Trust Services Criteria apply to all infrastructure models, but the controls look completely different. Vulnerability scanning, firewall rule reviews, physical access, and backup verification on bare metal require experience cloud-native consultants do not have.
The reverse is also true. A services firm operating inside client environments needs a consultant who can scope SOC 2 when the company does not own infrastructure. Default GRC platform controls assume the entity provisions identities and runs workloads. When that is not the case, every control needs customization or a justified not-applicable rationale.
Ask
How many engagements have you run on infrastructure similar to ours?
4. Do they separate build from operate?
SOC 2, especially Type 2, has two distinct phases that most companies do not plan for separately. The build phase designs and implements the security program. The operate phase runs the program through the observation period, collecting evidence, performing access reviews, managing vendors, and maintaining the cadences the auditor will evaluate.
A consultant who treats the engagement as a single project that ends with a readiness assessment is leaving you exposed for the hardest part. The observation period is where programs stall. Evidence stops being collected. Reviews get skipped. By the time the auditor arrives, the period is full of gaps.
Ask
What happens after the build phase? Who runs the program during the observation period? If the answer is your team, make sure your team has the bandwidth. If they do not, the consultant should offer an ongoing program management option.
5. What is their auditor relationship?
Good consultants work with reputable audit firms and make introductions. They know what specific auditors look for, how they evaluate evidence, and where they push back. A consultant who has never worked with the auditor you selected is learning on your engagement.
Ask
Which audit firms do you typically work with?
6. Do they handle the auditor communication?
The audit involves evidence requests, scope challenges, and pushback on control design. If the consultant steps back after the build, the CTO's workload spikes during audit season.
Ask
Who is the primary point of contact with the auditor during the audit?
7. How do they price the engagement?
Hourly billing creates perverse incentives. Scope creep benefits the consultant. Small questions become billable events.
Fixed-price engagements force accurate scoping upfront. Total cost known before work starts. For a detailed breakdown of what SOC 2 actually costs across all four components, see the cost and timeline guide.
Bundled packages (platform + audit + consulting under $15,000) should raise questions. Not enough dollar for real program design, and all the stakeholders involved. Even if everything is streamlined.
Ask
Fixed-price or hourly? What is included, what costs extra?
8. What do they hand over when the engagement ends?
The client should own everything: policies, control matrix, runbooks, evidence documentation, access review templates, playbooks and procedures, GRC platform configuration. No lock-in, no proprietary templates, no keep paying us to access your own docs.
Ask
If we bring the program in-house, what exactly do we walk away with?
Consultant vs Automated Compliance Platform: When Each Wins
A question that comes up in most first scoping calls: do we even need a consultant, or can the platform handle this? The honest answer is that the two are not alternatives. They do different jobs, and companies that treat them as interchangeable end up short on one side or the other.
What a GRC platform does well
- Automated evidence collection from cloud providers, identity platforms, HRIS, ticketing, and endpoint management.
- Control status dashboards and continuous monitoring.
- Policy template libraries for a starting point.
- Multi-framework cross-mapping so one control satisfies SOC 2 and ISO 27001 simultaneously.
- Auditor access portal and evidence hand-off.
What a GRC platform does not do
- Define your scope. The platform has no opinion on which systems, teams, or data should be in scope. Default scope from a platform setup is almost always wrong.
- Design controls that match your architecture. Default controls assume a generic SaaS-on-AWS deployment. Bare metal, hybrid cloud, services-inside-client-environments, and AI-specific workloads all need custom control design.
- Argue with the auditor. When the auditor pushes back on a control, the platform does not respond. Someone with framework literacy has to.
- Separate applicable from not-applicable and justify the choice. The Statement of Applicability and SOC 2 scope memo are human judgment calls.
- Build a security program. Evidence collection is not a program. Policies that match the company, controls that match the stack, and cadences that actually run are a program.
When platform-only is enough
A small, cloud-native SaaS company with a simple stack, a single production environment, no regulated data classifications beyond generic customer data, and a CTO with framework literacy can often run SOC 2 Type I on platform templates and clear the first audit. The cost: a report that passes but frequently does not survive enterprise procurement review, and a program that stops operating the day the platform subscription renews. And then renewal arrives — scope has crept, evidence has drifted, and the original platform fit no longer matches the company you've become.
When a consultant is non-negotiable
Any of the following makes platform-only a bad bet:
- On-prem, hybrid cloud, or colocation infrastructure (default controls do not apply).
- Services firm operating inside client environments (the entity does not own the infrastructure it is auditing).
- AI or ML systems in scope (platform controls do not yet cover ISO 42001-style AI governance).
- Enterprise buyers who read the full SOC 2 report and ask questions (platform-default reports read as such).
- Multi-framework scope (SOC 2 plus ISO 27001, HIPAA, or CPCSC) where control design matters across all of them.
- Tight audit timelines with no existing security program (platform setup takes weeks; building a program from scratch around it takes months).
The frame that works: the platform is a tool; the consultant is the expertise. Most companies need both. Platform-only works for the narrowest case. Consultant-only is possible but slower and more expensive than a consultant-plus-platform engagement.
How to Compare Two SOC 2 Consultants
When two consulting proposals land on the table, the checklist above is how to read them. The comparison rarely comes down to price alone. It comes down to eight questions applied to each proposal side by side.
- Scoping depth. Did each firm scope the engagement from your architecture, or from a template? The proposal that lists specific systems, data classifications, and team boundaries has done real work.
- Senior staffing. Which senior consultant will run the engagement, not just the sales call? Ask for a name and a bio.
- Infrastructure fit. Which firm has prior engagements that look like yours? On-prem, hybrid, services-based, AI-native, or multi-tenant SaaS each pulls in different implementation patterns.
- Build-to-operate handoff. Which proposal explicitly covers the observation period? Build without operate is half the engagement.
- Auditor relationships. Which firms does each consultant work with regularly, and do those firms fit your buyer expectations?
- Policy approach. Ask for a sample policy from a prior engagement. Is it a template with the company name swapped in, or is it clearly written for the specific environment?
- Deliverable ownership. What do you walk away with if you bring the program in-house after the build? Any proposal that keeps artifacts inside the consultant's system is a lock-in risk.
- Price structure. Fixed-price on a defined scope beats hourly almost every time. Hourly engagements optimize for billable hours, not program quality.
The consultant that wins on five or more of these rarely loses on the remaining three by enough to matter. The consultant that wins only on price usually loses on the rest.
Red Flags
Watch for these in any SOC 2 consulting proposal
- Audit-ready in two weeks. That means templates, not programs.
- Our platform handles everything. No platform designs controls, defines scope, or argues with auditors.
- We guarantee you will pass. No reputable consultant guarantees audit outcomes. The audit is independent.
- Junior staff running the engagement. Senior on the sales call, junior running the implementation.
- No mention of the observation period. Build without operate is half the problem.
The Condensed Checklist
☐ Leads with scoping questions, not a platform demo
☐ Customizes policies to the actual organization, not templates
☐ Has experience with the specific infrastructure model
☐ Explicitly plans for the build-to-operate transition
☐ Has established auditor relationships and handles audit communication
☐ Prices on fixed scope, not hourly
☐ Hands over all deliverables with no lock-in
☐ Puts a senior consultant on the engagement, not just the sales call
☐ Can explain what happens during the observation period
☐ Does not guarantee passage or promise unrealistic timelines
The SOC 2 report opens doors. The security program behind it determines whether those doors stay open. The consultant you choose determines which one you actually get.
Build an Effective Security Program
Fixed-price SOC 2 engagements led by senior consultants. Program first, audit second.
Frequently Asked Questions
How much should a SOC 2 consultant cost?
A competent SOC 2 consulting engagement (Build phase, 8-12 weeks) typically ranges from $20,000 for a single-framework SMB engagement to $75,000+ for enterprise scope. Bundled packages under $15,000 that include platform, audit prep, and audit should raise questions about the depth of program design included.
Can I do SOC 2 without a consultant?
Technically, yes. SOC 2 does not require a consultant. But the consultant designs controls, defines scope, writes policies that match the actual organization, and manages auditor communication. Companies that skip consulting often end up with a report based on default GRC platform controls that does not reflect how the business actually operates.
What is the difference between a SOC 2 consultant and a GRC platform?
A GRC platform automates evidence collection and tracks control status. A consultant designs the security program, determines scope, writes policies, and manages the auditor. The platform is a tool. The consultant is the expertise. Most companies need both.
How long does a SOC 2 consulting engagement take?
The Build phase (program design and implementation) takes 8 to 12 weeks. After that, the program needs to operate through an observation period (3-12 months for Type 2). The total timeline from kickoff to a Type 1 report is typically 3 to 6 months.
Should I hire a local SOC 2 consultant or work with a remote firm?
SOC 2 consulting is delivered remotely in almost all cases. What matters is the consultant's experience with your infrastructure model, your industry, and the audit firms you plan to use. Geography is less important than technical depth and auditor relationships.
How do I choose a SOC 2 provider for my SaaS company?
Choosing a SOC 2 provider for a SaaS company comes down to matching three things: the provider's technical depth against your architecture, their build-to-operate approach against your team's capacity to run the program after the engagement, and their pricing model against your procurement discipline. Start by deciding whether you need a GRC platform, a consultant, or both. For most SaaS companies the answer is both: the platform automates evidence, the consultant designs the program and manages the audit. Then evaluate each candidate against the eight-question checklist above, score them side by side, and pick the one that leads with scoping questions rather than a demo. The right SOC 2 provider should treat your SaaS architecture as the starting point, not as a variable to squeeze into a pre-built template.
Are SOC 2 consultants and ISO 27001 consultants different?
Many firms offer both, and most engagements that look pure SOC 2 end up touching ISO 27001 within the first year as soon as an enterprise deal in Europe appears. The underlying security program is the same. What differs is the framing, the documentation style, and the audit mechanics. Evaluate any consultant on their ability to run combined SOC 2 and ISO 27001 engagements, not just the framework you think you need today.
Ready to Start Your Compliance Journey?
Get a clear, actionable roadmap with our readiness assessment.
About the Author
Former security architect for Bank of Canada and Payments Canada. 20+ years building compliance programs for critical infrastructure.
How Ready Are You for SOC 2?
Score your security program in under 5 minutes. Free.
Take the Scorecard