A SOC 2 readiness assessment is not the audit. It is the diagnostic step that tells a company exactly where it stands before committing budget and engineering time to implementation. The assessment maps the current environment against SOC 2 requirements, identifies gaps, and produces a prioritized remediation roadmap. Done well, it eliminates the guesswork from the Build phase. Done poorly, it produces a generic checklist that creates more confusion than clarity.
The distinction matters because the assessment shapes every decision that follows: which Trust Services Criteria to include, how to define the scope boundary, whether to pursue Type 1 or Type 2 first, and what the implementation will actually cost in time and resources.
The Assessment Is Not the Audit
This is the most common source of confusion. A SOC 2 readiness assessment, sometimes called a gap assessment, is an internal exercise. No auditor is involved. No report is issued to customers. The output is a set of documents that a company uses to plan and execute implementation.
The audit comes later, conducted by a licensed CPA firm, and results in a formal SOC 2 report. The readiness assessment is what ensures that when the auditor arrives, the program is ready to withstand scrutiny.
Assessment vs. Audit
The assessment is the blueprint. The Build phase is construction. The audit is the inspection. Skipping the blueprint and jumping straight to construction is how companies end up rebuilding halfway through.
What a Good Assessment Covers
A thorough SOC 2 readiness assessment works through six areas. Each one produces a specific output that feeds directly into the implementation plan.
1. Scope Definition
The first step is defining what is actually in scope for SOC 2. This means identifying the system boundary: which products, infrastructure, teams, and data flows are included. Scoping decisions have the single largest impact on the cost and complexity of the entire engagement.
A company with multiple business units may only need to certify the SaaS product, not the entire organization. Identity groups, network segmentation, and data flow diagrams become the evidence that defines the boundary. The readiness assessment should produce a draft system description that the auditor will later use as the foundation for the SOC 2 report.
The assessment also determines which Trust Services Criteria apply. Security is always in scope. Availability, Processing Integrity, Confidentiality, and Privacy are optional and depend on the nature of the service and what customers are asking for. Adding criteria that are not contractually required increases scope, cost, and timeline without adding value.
2. Control Inventory
Once the scope is defined, the assessment maps the company's existing practices against SOC 2 control requirements. This is where the real picture emerges.
A common pattern across engagements: companies are already doing more than they realize. Development teams that link commits to tickets, run QA before deploying, and manage access through identity platforms are performing SOC 2-relevant activities daily. The gap is not in practice but in formalization and evidence. Under SOC 2 CC8.1, the auditor needs to see that changes are authorized, tested, and approved before deployment. If the team already does this in their issue tracker with commit references and QA sign-offs, the missing piece is usually documentation, not capability.
The Evidence Gap
The control inventory maps each SOC 2 criterion to one of three states: control exists and is documented, control exists but lacks documentation, or control does not exist. That third category is where the real implementation work lives.
3. Gap Identification
The gap analysis is the core deliverable. It answers a specific question: what needs to change between now and audit readiness?
Gaps fall into distinct categories:
Policy Gaps
No formal policy covering a required area, such as incident response, access management, or change management.
Process Gaps
A policy exists on paper but there is no operational process backing it, or the process does not match what the policy describes.
Evidence Gaps
The work is happening, but there is no trail for the auditor to follow. Patching happens weekly, but there are no tickets. Access is managed carefully, but there is no log of changes. This is one of the most frequent findings.
Technology Gaps
The infrastructure lacks a required capability, such as centralized logging, endpoint management, or vulnerability scanning.
Scope Gaps
Something that should be in scope was missed, or something in scope cannot be adequately controlled.
Each gap should be mapped to the specific SOC 2 criteria it affects. A gap in access review processes maps directly to CC6.2. A gap in security documentation maps to CC1.1 through CC1.4. This mapping is what turns a generic checklist into an actionable plan.
4. Remediation Roadmap
The gap report without a remediation plan is just a list of problems. The roadmap takes each gap and assigns it a priority, an estimated level of effort, a responsible party, and a target completion date.
Prioritization matters because not all gaps carry equal weight. A missing incident response plan is a high-priority gap because it affects multiple SOC 2 criteria and is one of the first things an auditor reviews. A missing visitor log for an office that uses badge access is low priority and can be addressed with a simple process addition.
The roadmap should sequence work in a logical order. Foundational items come first: scope finalization, policy framework, GRC platform configuration. Then come the control implementations that depend on those foundations. Evidence collection mechanisms should be running before the observation period begins, because retroactive evidence does not satisfy SOC 2 Type 2 requirements.
5. Timeline Estimate
A readiness assessment should produce a realistic timeline for reaching audit readiness. This depends on several factors: the number and severity of gaps, the team's available bandwidth, whether the company is targeting Type 1 or Type 2 (companies with tight deadlines often target Type 1 in 90 days), and whether external support is part of the plan.
| Starting Position | Typical Build Timeline | Primary Work |
| No formal security program | 8 to 14 weeks | Full program build from the ground up |
| Partial program (some policies, inconsistent tooling) | 6 to 10 weeks | Untangling existing artifacts, filling gaps |
| Mature practices, no SOC 2 documentation | 4 to 8 weeks | Formalizing and documenting what already exists |
The timeline should account for the fact that SOC 2 implementation is not the only thing the engineering and operations teams are doing. Realistic estimates build in the reality that this work competes with product development, customer commitments, and everything else on the roadmap.
6. Auditor Recommendations
A good readiness assessment includes guidance on selecting an audit firm. Not all auditors are the same. Some specialize in technology companies and understand cloud-native architectures. Others come from a traditional audit background and may require extensive documentation for controls that are standard in modern engineering environments.
The assessment should recommend auditors based on the company's specific architecture, size, and compliance goals. It should also flag any areas where the auditor selection could affect scope or timeline.
What a Bad Assessment Looks Like
A bad readiness assessment is a generic checklist with pass/fail indicators and no context. It asks whether a company has an incident response plan (yes/no) without examining whether the plan reflects the company's actual environment, team structure, or technology stack.
Red Flags in a Readiness Assessment
No scope definition before evaluation. Pass/fail with no prioritization. Template recommendations that ignore the company's architecture. No timeline or cost context. No connection to the Build phase. Companies that receive this kind of assessment often end up redoing the work during implementation.
The Output Artifacts
A completed readiness assessment should produce four deliverables:
Assessment Deliverables
- Gap report - detailed findings mapped to specific SOC 2 criteria, categorized by gap type, with severity ratings
- Scope statement - draft system description defining the system boundary, applicable Trust Services Criteria, and in-scope people, processes, and technology
- Remediation roadmap - prioritized plan with estimated effort, responsible parties, dependencies, and target dates
- Build phase estimate - cost and timeline projection for the implementation work required to reach audit readiness
These four documents become the foundation for every decision in the Build phase. They answer the questions that matter: what needs to happen, in what order, how long will it take, and what will it cost.
How the Assessment Connects to Build and Operate
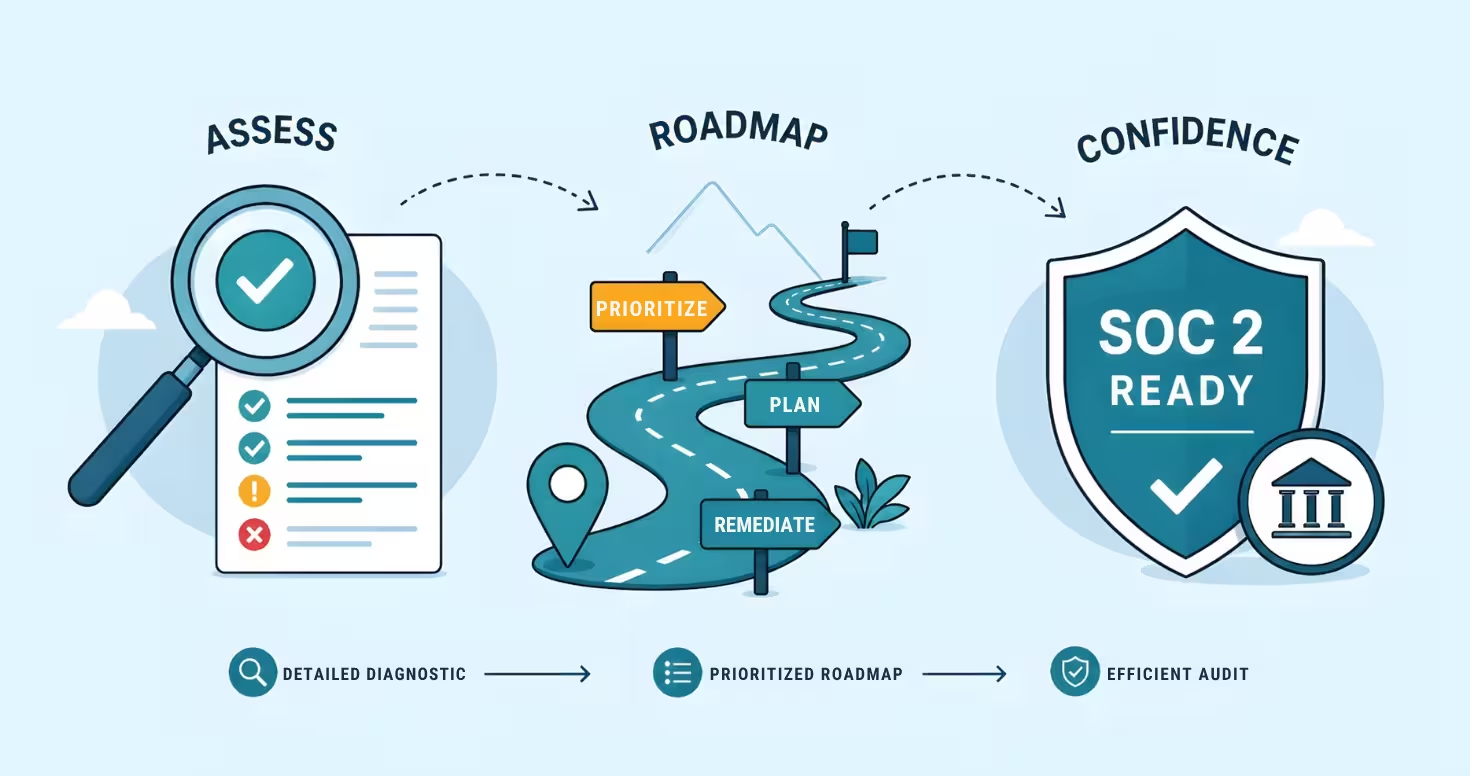
The readiness assessment is the first phase of a three-phase engagement structure: Assess, Build, Operate.
The Assess phase produces the gap report and roadmap. The Build phase executes the roadmap: writing policies, implementing controls, configuring the GRC platform, establishing evidence collection workflows, and preparing for the auditor. The Operate phase is where the program runs on an ongoing basis, executing the cadences (access reviews, vulnerability scans, policy updates) that produce the continuous evidence a Type 2 audit requires.
Each phase feeds the next. Without a solid assessment, the Build phase is guesswork. Without a well-executed Build, the Operate phase has nothing to sustain. And without ongoing operations, the program drifts, the evidence stops flowing, and the next audit becomes a scramble.
The most expensive mistake in SOC 2 is treating the assessment as a formality and rushing into implementation. The second most expensive mistake is treating implementation as the finish line and not planning for ongoing operations.
What to Look for in a Consultant
Not every SOC 2 readiness assessment delivers the same depth. When evaluating a consultant for the assessment phase, look for:
- Architecture-specific analysis - the assessment should reflect the company's actual technology stack, not a generic cloud checklist
- Prioritized output - gaps should be ranked by impact on audit readiness, not listed alphabetically
- Build phase connection - the assessment should be explicitly designed to feed into implementation
- Auditor relationship - consultants who work regularly with SOC 2 auditors understand what auditors actually look for and where teams commonly stumble
- Clear cost boundaries - the assessment phase should have a fixed scope and price, separate from the Build phase
The readiness assessment is the point where the company gets the clearest picture of what SOC 2 compliance will actually require. It is worth investing in the depth and rigor that produces a reliable answer.
Know Where You Stand
We build effective security programs that make compliance a byproduct, not a project.
Frequently Asked Questions
What is a SOC 2 readiness assessment?
A SOC 2 readiness assessment is a diagnostic evaluation that maps a company's current security posture against SOC 2 requirements. It identifies gaps in policies, processes, evidence, and technology, then produces a prioritized remediation roadmap. It is not the audit itself, but the preparation step that determines what needs to happen before an auditor arrives.
How long does a SOC 2 readiness assessment take?
The assessment phase itself typically takes two to four weeks, depending on the complexity of the environment and the number of systems in scope. The implementation work that follows the assessment (the Build phase) ranges from four to fourteen weeks based on the number and severity of gaps identified.
What is the difference between a readiness assessment and a gap assessment?
The terms are used interchangeably. Both refer to the process of evaluating a company's current state against SOC 2 requirements and identifying what needs to change before the audit. Some consultants use gap assessment to describe a narrower evaluation and readiness assessment for a more comprehensive engagement that includes scope definition and remediation planning.
What does a SOC 2 readiness assessment cost?
Assessment costs vary based on the size of the environment, number of systems in scope, and depth of analysis. A thorough assessment that includes scope definition, control inventory, gap analysis, remediation roadmap, and Build phase estimate is typically priced as a fixed-fee engagement separate from implementation. This separation allows the company to evaluate findings before committing to the Build phase.
Can a company do a SOC 2 readiness assessment internally?
Technically yes, but the value of an external assessment comes from objectivity and experience across multiple engagements. Internal teams tend to overestimate their readiness because they know the intent behind their practices without recognizing where the evidence falls short. An experienced consultant has seen the patterns that trip up auditors and can identify gaps that internal teams overlook.
What happens after the readiness assessment?
The assessment feeds directly into the Build phase, where the remediation roadmap gets executed. This includes writing policies, implementing controls, configuring the GRC platform, and establishing evidence collection workflows. Once the Build phase is complete, the company is ready for the audit (Type 1) or the start of the observation period (Type 2).
Ready to Start Your Compliance Journey?
Get a clear, actionable roadmap with our readiness assessment.
About the Author
Former security architect for Bank of Canada and Payments Canada. 20+ years building compliance programs for critical infrastructure.
How Ready Are You for SOC 2?
Score your security program in under 5 minutes. Free.
Take the Scorecard