When the second framework arrives, most teams make the same mistake.
The first one, usually SOC 2, took nine to twelve months and a large chunk of the engineering org's attention. Then a customer in the EU asks for ISO 27001. A federal contract opportunity needs CPCSC. A hospital partner wants HIPAA assurances. A new AI feature pulls ISO 42001 into the conversation.
The temptation, every time, is to treat the new framework as a new project. New gap assessment, new policies, new evidence pipelines, new auditor, another nine to twelve months. The cost compounds. Engineers get pulled off product work repeatedly. Policies start contradicting each other because nobody has the time to reconcile three dialects of the same control.
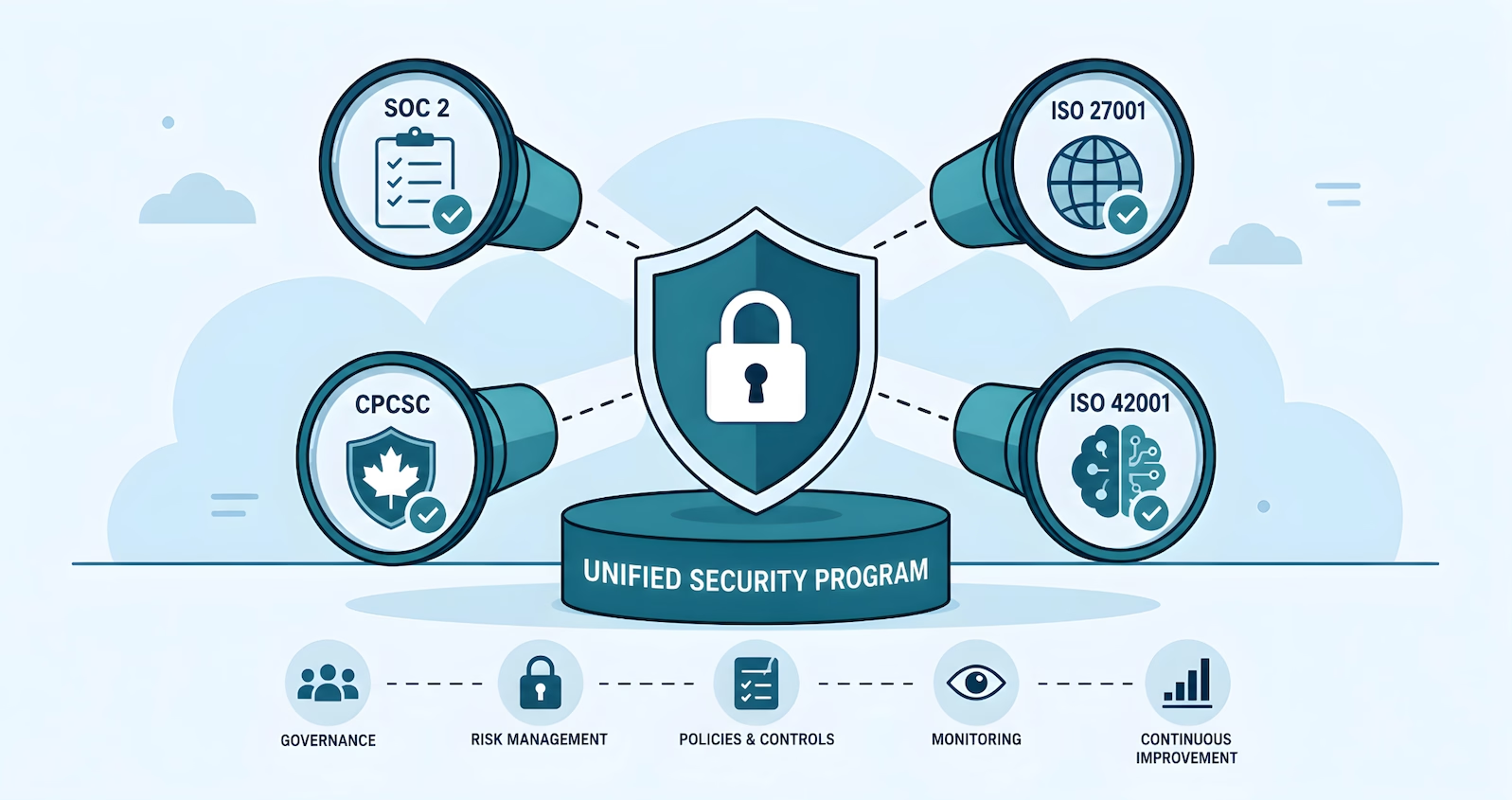
The core idea
Build one security program. Point frameworks at it as lenses. Every modern compliance standard is asking about the same twelve operational domains. Frameworks are how the world checks your work. They are not the work.
The foundation that lives underneath every framework
Strip the framework labels off and look at what every modern compliance standard is asking about. The list is short, and it has not changed much in a decade.
- Identity and access management. Who has accounts, what those accounts can do, how access is granted, reviewed, and revoked.
- Authentication. How users and devices prove who they are, including MFA on anything that matters.
- Data classification and handling. What information exists, where it lives, who can touch it, how it leaves the company.
- Endpoint protection. Devices are configured, patched, monitored, and can be wiped.
- Network and boundary protection. Edges are defined, traffic is controlled, public systems are separated from internal ones.
- Vulnerability and patch management. Flaws get found, prioritized, and fixed on a defensible cadence.
- Logging and monitoring. Activity is captured, retained, and reviewed; anomalies have a path to a human.
- Incident response. A plan exists, people know their roles, the plan has been exercised.
- Change and configuration management. Production changes are reviewed, tracked, and reversible.
- Vendor and third-party risk. Suppliers with access to data or systems are evaluated and monitored.
- Awareness and training. People know the rules and have been told why they exist.
- Governance. Someone owns security, decisions get documented, the program has a cadence.
SOC 2 asks about it. ISO 27001 asks about it. CPCSC asks about it. ISO 42001 asks about it and adds AI-specific governance on top. PIPEDA, Law 25, HIPAA, and GDPR all ask about it through a privacy lens but rest on the same operational reality.
What building once looks like
Building once means producing one coherent set of artifacts that can be pointed at any framework without rewrites.
One set of policies, written in plain operational language, not framework jargon. The access management policy describes how the company grants and reviews access. It does not start with In accordance with TSC CC6.1. When the SOC 2 auditor asks about CC6.1, the same policy maps cleanly. When the ISO 27001 auditor asks about Annex A 5.15, it maps cleanly again.
One access model. Groups by role. Provisioning tied to the HRIS. Quarterly reviews owned by a named person. Offboarding triggered by the same workflow regardless of which framework classifies the system.
One offboarding SLA. The leaver's accounts get disabled within the window the strictest applicable framework requires. CPCSC expects notification within 24 hours of termination, so the workflow notifies within 24 hours, full stop. SOC 2 is satisfied. ISO 27001 is satisfied. CPCSC is satisfied. The team does not maintain three different SLAs.
One logging stack. Centralized collection. Retention long enough to satisfy the strictest framework in scope. Alerting tuned to the actual threat model. Auditors get pointed at the same evidence repository regardless of which standard they are testing.
One vendor inventory with risk tiers, reassessment cadences, and contract clauses that map to multiple frameworks at once. One incident response runbook, exercised on a real cadence. One configuration baseline per platform, version-controlled, deviation-flagged.
Done this way, the program is documented in the language of how the company actually operates. Frameworks become a translation layer applied at audit time, not a constraint that shapes operations.
A worked example: one foundation, three audits
Take access management. Foundation: a documented joiner-mover-leaver process tied to the HRIS, role-based groups, MFA on everything that matters, quarterly access reviews, an audit log of provisioning actions.
- SOC 2 reads this through CC6.1, CC6.2, and CC6.3.
- ISO 27001 reads it through Annex A 5.15, 5.16, 5.17, 5.18, and 8.2.
- CPCSC Level 1 reads it through control 03.01.01, which expects account types defined, lifecycle managed, authorized users specified, accounts disabled within 90 days of inactivity, and notification within 24 hours when a user is terminated.
One workflow. Three sets of evidence pulled from the same source.
The same logic applies to patch management. One scanning program with SLAs set against the strictest applicable framework (30 days for high-risk flaws under CPCSC control 03.14.01) satisfies SOC 2 CC7.1 and CC8.1, ISO 27001 Annex A 8.8 and 8.32, and CPCSC in a single stroke.
The pattern repeats across every domain. Boundary protection. Malicious code defense. Media sanitization. Physical access. Incident response. Build the foundation against the strictest applicable framework, document it in operational language, and the rest is mapping.
The full argument for an effective security program
Effective Security First is our field report on building one security program that multiple frameworks map to, instead of three parallel programs nobody wants to maintain. Download the PDF.
Where the 20-30% delta lives
Foundation-first does not mean every framework after the first is free. There is a real delta. It lives in a narrower place than most teams expect.
Three things drive it. Evidence formats: SOC 2 sampling across the audit period, ISO 27001 ISMS documentation and management review minutes, CPCSC self-assessment attached to the CanadaBuys profile. Same activity, different packaging. Terminology: a control in SOC 2 is not the same artifact as in ISO 27001 Annex A or CPCSC. The Statement of Applicability is ISO 27001. The System Security Plan is CPCSC and CMMC. Translating takes effort. Genuinely unique controls: ISO 27001's formal ISMS with internal audit cycle, CPCSC's Specified Information scoping, ISO 42001's AI impact assessments. Real additions, but bounded.
The remainder is audit prep and walking the auditor through evidence that already exists. Second and third frameworks tend to land in the 20-30% range of effort relative to the first. Most of that is paperwork, not program rebuild.
When framework-first is the right call
Foundation-first is not universal. There are cases where building directly to one framework makes sense.
A company in a single regulated environment, where one framework will dominate every customer conversation and no other standards are on the horizon, can reasonably build to that framework directly. A defence contractor that will only ever handle Specified Information should optimize for CPCSC. A US healthcare-only SaaS should optimize for HIPAA.
Time pressure also changes the math. If a single contract worth meaningful revenue requires SOC 2 in 90 days and nothing else is pending, drive to SOC 2 and worry about generalizing later. The foundation can be retrofitted on the way out.
For most companies, the second framework is visible on the roadmap when the first one starts. Enterprise buyers ask about SOC 2 and ISO 27001. Canadian government opportunities require CPCSC. AI features pull in ISO 42001. Privacy regimes overlap with all of them. Building three programs in parallel is a choice, and usually the wrong one.
Frequently Asked Questions
If we already have SOC 2, how much extra work is ISO 27001?
If the SOC 2 program was built foundation-first, ISO 27001 typically lands in the 20-30% range of incremental effort. The big additions are the formal ISMS documentation, the Statement of Applicability, the risk treatment plan, and the internal audit cycle. If the SOC 2 program was built framework-first with policies that explicitly cite TSC language, the delta can climb to 40-50% because policy language and evidence formats need to be reworked.
Can one security program cover SOC 2, ISO 27001, and CPCSC at the same time?
Yes, if the program is designed against the strictest applicable requirement in each domain. CPCSC sets a 24-hour notification window for terminations, so the offboarding SLA becomes 24 hours. CPCSC sets a 30-day patch SLA for high-risk flaws, so the patch SLA becomes 30 days. The program meets the strictest bar and is, by construction, compliant with the looser ones.
Where does GRC tooling fit in this approach?
GRC platforms are excellent at storing evidence, tracking control status, and generating auditor-ready reports across multiple frameworks. They are necessary infrastructure past a certain size. A foundation-first program in a GRC platform produces clean cross-framework reporting almost for free. A framework-first program in the same platform produces three parallel control libraries nobody wants to maintain.
What if a customer asks for a framework we have not built for yet?
Run a gap assessment against the new framework using the existing program as the starting point. Gaps are usually small if the foundation is in place: framework-specific documentation, one or two unique controls, an audit prep cycle. The honest answer to the customer is usually a defensible timeline measured in months, not a panic project.
Ready to Start Your Compliance Journey?
Get a clear, actionable roadmap with our readiness assessment.
About the Author
Former security architect for Bank of Canada and Payments Canada. 20+ years building compliance programs for critical infrastructure.
How Ready Are You for SOC 2?
Score your security program in under 5 minutes. Free.
Take the Scorecard