Every other control family in ITSP.10.171 has a reasonable analogue in the commercial compliance world. Access control maps to SOC 2 CC6. Incident response maps to CC7. Audit logging, encryption, configuration management, all of it has some equivalent in the frameworks that cloud-native companies already operate under.
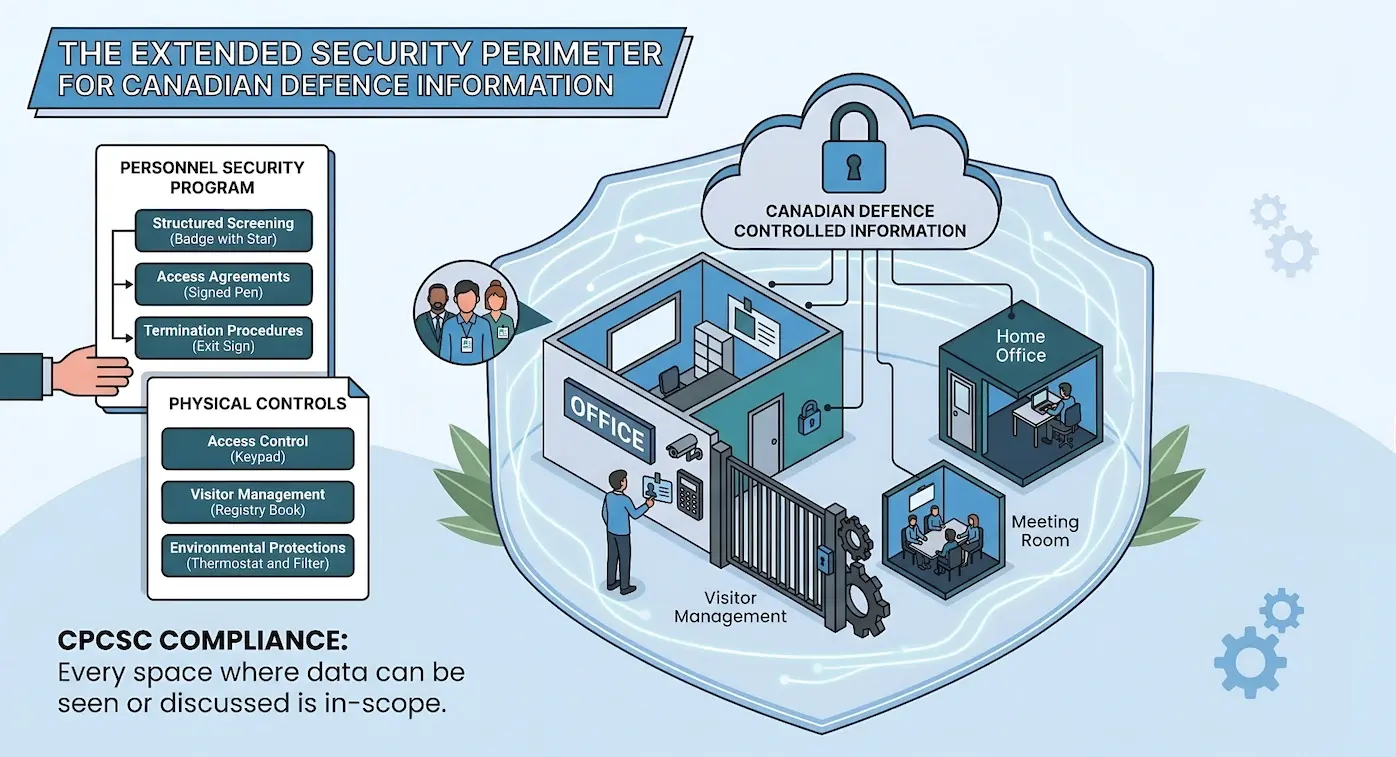
Physical Protection (PE) and Personnel Security (PS) are different. These are two families where companies coming from a SaaS or cloud-first background tend to have significant gaps, because their entire operating model was built around not needing physical controls. The office is a WeWork. The data centre is AWS. The screening process is a reference check and an offer letter. None of that satisfies what CPCSC requires when controlled information enters the picture.
This post breaks down the PE and PS control families from ITSP.10.171, explains why they represent the sharpest departure from commercial frameworks, and covers what organizations actually need to implement.
Why Physical and Personnel Controls Are the Biggest Gap
The cloud-native operating model was designed, correctly, to abstract away physical infrastructure. When an application runs in a managed cloud environment, the cloud provider handles facility security, power redundancy, fire suppression, and physical access control. The shared responsibility model is well understood: the provider secures the infrastructure, the customer secures the data and applications running on it.
That abstraction breaks down when an organization handles controlled information under CPCSC. The certification does not care whether the servers are in a data centre or a closet. It cares about every physical location where controlled information is processed, stored, or discussed, and that includes offices, home offices, and any alternate work site where employees access the information.
The Cloud Provider Gap
Companies with SOC 2 or ISO 27001 certifications often assume they have physical security covered because their cloud provider passed its SOC 2 audit. That covers the infrastructure layer. It does not cover the laptop sitting open in a co-working space where an engineer is reviewing a defence contract deliverable.
Personnel security follows the same pattern. Commercial frameworks expect access reviews, role-based permissions, and termination checklists. CPCSC expects documented screening before granting access to controlled information, formal access agreements signed by each individual, and structured procedures for personnel transfers and terminations that go beyond disabling an account.
Physical Protection (PE) Controls
The PE family in ITSP.10.171 addresses how organizations control physical access to facilities and protect the environments where controlled information exists. These controls derive from the NIST 800-171 PE family, adapted for the Canadian defence supply chain context.
Access Authorizations and Physical Access Control
Organizations must limit physical access to systems and facilities that process controlled information to authorized individuals. This requires a documented authorization process: who is allowed access, what areas they can enter, and how that access is granted and revoked.
For a company that operates primarily from cloud infrastructure, the facility question often reduces to the corporate office and individual home offices. But the control is broader than it first appears. If controlled information is displayed on screens, discussed in meetings, or printed for review, the room where that happens is a controlled area, and physical access to that area must be managed.
In practice, this means:
- Defined secure areas where controlled information is processed, with access restricted to authorized personnel
- Physical access mechanisms such as badge readers, key systems, or access logs for controlled areas
- An authorization list that is reviewed and updated as personnel change roles or leave the organization
- Access logs that record who entered controlled areas and when
Shared Office Spaces
A co-working environment where desks are open and meeting rooms are bookable by anyone does not satisfy PE requirements for controlled areas. This does not necessarily mean leasing dedicated space, but it does mean designating specific, access-controlled areas for defence-related work.
Visitor Access Management
Visitor access is a control that rarely exists in cloud-native companies because there has been no reason for it to exist. ITSP.10.171 requires that visitors to facilities where controlled information is processed are escorted, their access is documented, and visitor activity logs are maintained.
The requirements include:
- Visitor logs that record the name of the visitor, the organization they represent, the individual they are visiting, and the date and time of the visit
- Escort procedures ensuring visitors are accompanied by authorized personnel in controlled areas
- Visitor identification that distinguishes visitors from authorized personnel (badges, lanyards, or similar markers)
For organizations that have never tracked visitor access, implementing this requires both a process and a physical mechanism. A sign-in sheet at reception is the minimum. Digital visitor management systems offer more structure, but the control is about the process, not the technology.
Power Equipment and Fire Protection
These controls require organizations to protect facility power equipment and apply fire protection mechanisms for facilities containing controlled information. For most companies in the defence supply chain, this translates to ensuring that the areas where controlled systems operate have appropriate power protection (UPS, surge protection) and fire detection or suppression appropriate to the environment.
Companies relying entirely on cloud infrastructure often overlook this because they associate power and fire protection with data centres. But if on-premises equipment processes controlled information, even a single workstation in a locked room, the facility housing that equipment needs appropriate environmental protections.
Alternate Work Site Considerations
This is the control that creates the most friction for organizations with remote or hybrid workforces. ITSP.10.171 requires that organizations verify the security of alternate work sites, which includes home offices where employees access controlled information.
Verification means confirming that the alternate work site provides adequate physical security for the controlled information being processed there. In practical terms:
- Dedicated workspace where controlled information can be accessed without exposure to unauthorized individuals (including family members or roommates)
- Screen privacy measures to prevent visual disclosure
- Secure storage for any physical materials containing controlled information
- Network security appropriate for processing controlled information (not the coffee shop Wi-Fi)
This does not mean every remote worker needs a SCIF in their basement. It means the organization must assess and document the conditions under which remote access to controlled information is acceptable, and verify that individual work sites meet those conditions.
Personnel Security (PS) Controls
The PS family addresses the human element: ensuring that the people who access controlled information are screened, understand their responsibilities, and are properly managed through the lifecycle of their employment.
Updated April 14, 2026 — Final CPCSC Level 1 Requirements
Are you ready for CPCSC Level 1?
Take the scorecard to find out.
Personnel Screening
ITSP.10.171 requires that organizations screen individuals before authorizing access to systems that process controlled information. The screening must be commensurate with the sensitivity of the information and the risk associated with the individual's role.
For many defence contracts, this aligns with existing Government of Canada security screening requirements (Reliability Status or Secret clearance). But the PS controls in ITSP.10.171 apply to the organization's own screening process, independent of government security clearances. This means:
- Background checks conducted before granting access, proportionate to the role
- Rescreening at defined intervals or when there is a change in risk factors
- Documentation of screening decisions and the basis for granting access
Companies coming from commercial frameworks often have a hiring process that includes reference checks and possibly a criminal background check. CPCSC screening requirements are more structured: the screening must be documented, the criteria must be defined in advance, and the results must be retained as evidence of compliance.
Screening vs. Clearance
Government security clearances (Reliability Status, Secret) and organizational screening under ITSP.10.171 are separate requirements. Having a cleared employee does not exempt the organization from conducting and documenting its own screening process.
Access Agreements
Before any individual accesses controlled information, they must sign a documented acknowledgement of their security responsibilities. This is a formal agreement, not an onboarding checkbox in an HR system.
The access agreement must cover:
- The individual's responsibilities for protecting controlled information
- Acceptable use conditions for systems that process controlled information
- Consequences of non-compliance with security requirements
- Acknowledgement that the individual has read and understands the organization's security policies
These agreements must be signed before access is granted and updated when security policies change. Organizations need to maintain a record of signed agreements and ensure that individuals who have not signed, or whose agreements have lapsed, do not have access to controlled systems.
Termination Procedures
When an individual leaves the organization or transfers to a role that no longer requires access to controlled information, the organization must follow documented termination procedures. This goes beyond disabling the user's account.
The requirements include:
- Immediate revocation of physical and logical access to controlled information upon termination
- Retrieval of all organization-owned assets (devices, badges, keys, tokens)
- Exit interview covering the individual's ongoing obligations regarding controlled information
- Documentation of the termination process and all actions taken
Involuntary Terminations
For involuntary terminations, the timing and sequence matter. Access must be revoked before or concurrently with notification, not after. Organizations that rely on a ticketing system to process offboarding over several days will need to tighten the procedure for personnel with access to controlled information.
Personnel Transfers
Internal transfers also require attention. When an individual moves from a role that required access to controlled information to one that does not, the access must be reviewed and adjusted within a defined period. This prevents the accumulation of access rights that is common in organizations where role changes happen informally.
How This Differs from Commercial Frameworks
SOC 2 and ISO 27001 both address physical security and personnel management, but at a different level of specificity.
| Control Area | SOC 2 / ISO 27001 | CPCSC (ITSP.10.171) |
| Physical access | SOC 2 CC6.4 covers restrictions; cloud provider SOC 2 accepted for infrastructure | Every location where controlled info is processed must have access controls, including offices and home offices |
| Visitor management | Expected in high-security environments but not universal across audits | Mandatory visitor logs, escort procedures, and visitor identification |
| Personnel screening | ISO A.6 covers screening and terms; SOC 2 expects reasonable hiring practices | Documented criteria, screening before access, rescreening at intervals, evidence retained |
| Access agreements | Acceptable use policies during onboarding | Formal signed agreements specific to controlled information, updated when policies change |
| Termination | Offboarding checklists, account deprovisioning | Immediate access revocation, asset retrieval, exit interview, full documentation |
| Alternate work sites | Remote work policies but no physical verification | Documented assessment of each home office for physical security, screen privacy, secure storage |
The net effect is that a company with a mature SOC 2 or ISO 27001 program will have a foundation to build from, but will almost certainly have gaps in visitor management, formal personnel screening documentation, alternate work site verification, and structured access agreements. These are the areas where the transition from commercial to defence compliance requires new processes, not just enhanced existing ones.
Common Gaps for Cloud-Native Organizations
Based on what is typical for companies entering the defence supply chain from a commercial background, gaps that consistently appear include:
No visitor management process
The office does not have a visitor log, escort procedure, or visitor identification mechanism because there has never been a reason to track who visits.
No formal personnel screening beyond hiring
Background checks may happen as part of hiring, but there is no documented screening policy, no defined criteria, and no rescreening process.
No structured termination procedure for controlled information
Offboarding follows a general IT checklist, not a security-specific procedure that accounts for controlled information access.
No alternate work site assessment
Remote work is allowed by policy but there is no verification that home offices meet physical security requirements for processing controlled information.
No signed access agreements
Employees may acknowledge an acceptable use policy during onboarding, but there is no specific agreement covering controlled information responsibilities.
Shared or open office environments
The workspace does not have designated controlled areas because the company has never needed to restrict physical access within its own office.
Each of these gaps requires a process, not a tool. There is no SaaS platform that will generate a visitor log or verify a home office. These are operational controls that require policy development, training, and ongoing management.
Implementation Approach
For organizations that need to build PE and PS controls from a minimal baseline, the implementation sequence matters.
Start with policy. Draft the physical security policy and personnel security policy before implementing any specific controls. These policies define what the controls need to achieve and provide the basis for documentation.
Define controlled areas. Identify every location where controlled information is or will be processed, stored, or discussed. This includes the office, individual home offices, and any travel or temporary work locations. Determine what physical security measures each location requires.
Implement access controls for the office. If the office does not have access-controlled areas, this is the first physical investment. Badge readers or electronic locks for rooms where controlled information is processed. An access list that is reviewed quarterly.
Build the visitor management process. A visitor log, an escort procedure, and visitor identification. This can start as a paper-based process and move to a digital system as the organization matures.
Formalize personnel screening. Define screening criteria for roles that require access to controlled information. Establish a process for conducting and documenting background checks. Set rescreening intervals.
Create access agreements. Draft the access agreement template, have legal review it, and implement a process for distributing, signing, and tracking agreements. Integrate this into the onboarding workflow.
Update termination procedures. Add controlled information-specific steps to the offboarding checklist. Define the timing requirements for access revocation. Test the process with a tabletop exercise.
Assess alternate work sites. Create an assessment checklist for home offices and remote work locations. Conduct assessments for all personnel who access controlled information remotely. Document the results and any conditions placed on remote access.
Updated April 14, 2026 — Final CPCSC Level 1 Requirements
Are you ready for CPCSC Level 1?
Take the scorecard to find out.
Frequently Asked Questions
Does CPCSC require a dedicated secure facility?
Not necessarily. CPCSC Level 1 requires that organizations limit physical access to systems and facilities where controlled information is processed. For many organizations, this means designating specific areas within an existing office as controlled areas with appropriate access restrictions, rather than building or leasing a dedicated secure facility. The requirement is proportionate to the sensitivity of the information and the organization's operations.
How does remote work interact with CPCSC physical security requirements?
ITSP.10.171 includes alternate work site controls that require organizations to verify the physical security of any location where controlled information is accessed. Remote work is not prohibited, but the organization must assess each alternate work site and document that it meets the physical security requirements. This typically involves a home office assessment covering dedicated workspace, screen privacy, secure storage, and network security.
If we already have SOC 2, what PE and PS gaps should we expect?
The most common gaps are visitor management (SOC 2 auditors rarely require formal visitor logs for standard office environments), documented personnel screening procedures (beyond what HR runs during hiring), formal access agreements specific to controlled information, and alternate work site verification. SOC 2 provides a foundation for physical and personnel controls, but CPCSC requires more structured documentation and specific procedures that commercial audits typically do not examine in depth.
Do personnel screening requirements apply to contractors and subcontractors?
Yes. Any individual who accesses controlled information must be screened before access is granted, regardless of their employment relationship with the organization. For contractors and subcontractors, this means the screening process must extend beyond full-time employees to include all personnel with access, and access agreements must be signed by each individual.
Next Steps
Physical and personnel controls are process-heavy and documentation-intensive, but they are not technically complex. The challenge is building the operational discipline for controls that did not previously exist in the organization.
For companies preparing for CPCSC certification, PE and PS are families to address early because they require organizational change, not just technical configuration. PE is expected to be part of Level 1 self-assessment, while PS applies at Level 2 under the full ITSP.10.171 standard. Starting with policy development and working through the implementation sequence gives the organization time to build these practices before attestation.
Truvo Cyber builds security programs for organizations entering the defence supply chain. If your team is navigating CPCSC requirements and needs help identifying gaps in physical security or personnel controls, contact us for an assessment.
Ready to Start Your Compliance Journey?
Get a clear, actionable roadmap with our readiness assessment.
About the Author
Former security architect for Bank of Canada and Payments Canada. 20+ years building compliance programs for critical infrastructure.
Ready for CPCSC Level 1?
Score your readiness across the 6 expected control families. Free.
Take the Scorecard