The previous twelve posts in this series covered the technical and operational control families in ITSP.10.171: access control, incident response, configuration management, supply chain risk, and everything in between. Each of those families requires documented policies, defined procedures, and personnel who understand their responsibilities. Governance is what ties all of that together.
It is tempting to treat governance and training as administrative overhead, the paperwork layer that sits on top of the real security work. That instinct is understandable, but it misses the point. Without a governance framework, the other sixteen control families in ITSP.10.171 are disconnected activities. Access reviews happen in one system, incident response operates from a different playbook, and configuration baselines exist in a spreadsheet that nobody updates. Governance is the structure that turns individual controls into a coherent program.
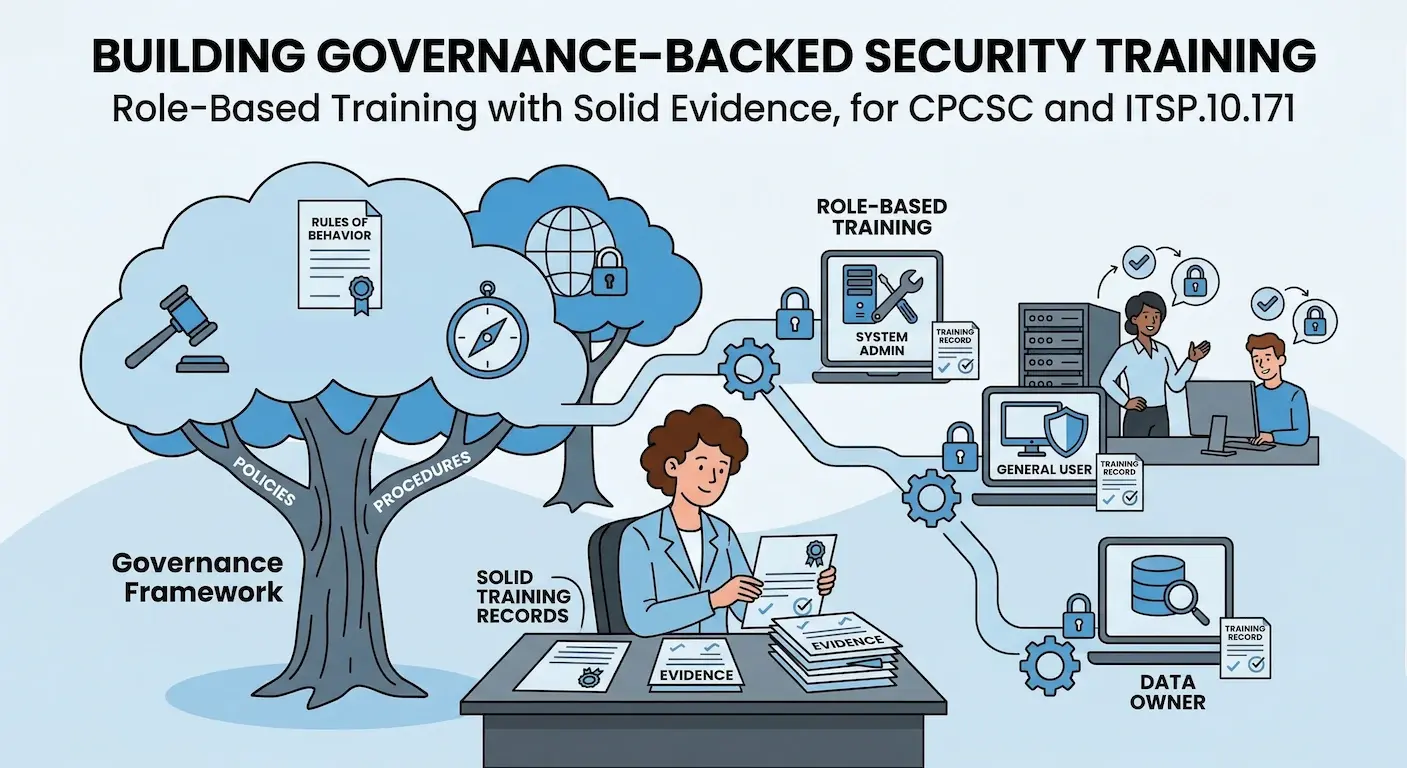
Why Governance Matters
The Awareness and Training (AT) family is the smallest control family in ITSP.10.171, but it carries weight during assessment because it reveals whether the security program is operationalized or merely documented. An assessor looking at training records is not checking a box. They are forming an opinion about whether the people operating the controls actually understand what they are doing and why.
The Awareness and Training (AT) Family in ITSP.10.171
The AT family in ITSP.10.171 covers three distinct areas: security awareness for all users, role-based training for personnel with security responsibilities, and maintenance of training records. Each area has specific assessment objectives that go beyond the typical annual phishing simulation.
Security Awareness Training
The standard requires that all system users, including managers, senior executives, and contractors, receive security awareness training as part of initial training for new users and on an ongoing basis thereafter. The training must cover the organization's security policies, rules of behavior, and the specific threats relevant to the organization's environment.
This is not a pass-fail checkbox. The expectation is that awareness training is tailored to the organization's actual risk environment. A defence contractor handling controlled information faces different threats than a consumer SaaS company, and the training content should reflect that difference. Generic vendor-provided awareness modules that cover password hygiene and email phishing are a starting point, but they are not sufficient on their own if the organization handles information subject to ITSP.10.171 requirements.
Role-Based Training
Role-based training is where the standard gets specific and where most organizations have a gap. ITSP.10.171 requires that personnel with security responsibilities, which includes system administrators, incident responders, and anyone handling controlled information, receive training specific to their assigned roles.
The distinction matters. General awareness training teaches all employees to recognize a phishing email. Role-based training teaches the incident response team how to handle a breach involving controlled information, teaches system administrators how to maintain configuration baselines, and teaches data handlers how to apply marking and dissemination controls.
NIST Lineage
This requirement traces back to NIST 800-171 AT-3, which explicitly calls for role-based training. The common failure mode is organizations where everyone, from the front desk to the security operations team, completes the same annual awareness module and that is the entire training program.
Training Records
The standard requires organizations to document and monitor security awareness training activities. This means maintaining records of who was trained, when they were trained, what the training covered, and evidence of completion. For role-based training, the records should also show that the training was relevant to the individual's specific responsibilities.
Training records serve two purposes. During a CPCSC assessment, they are direct evidence that the AT controls are operating. More practically, they protect the organization when something goes wrong. If an incident occurs because an administrator misconfigured a system, the training record demonstrates whether that person had been trained on the relevant procedures.
The Governance Framework: Policy vs. Procedure
Governance under ITSP.10.171 is not a single document. It is a framework of policies, procedures, and rules of behavior that define how the organization operates its security program. Getting the structure right matters more than getting the content perfect on the first pass, because a well-structured governance framework is maintainable and a poorly structured one is not.
The Policy-Procedure Distinction
A common structural mistake in governance frameworks is mixing policy statements with step-by-step procedures in a single document. Policies state commitments: what the organization will do, what standards it will maintain, and who is responsible. Procedures contain the operational detail: specific system names, step-by-step instructions, and configuration parameters.
Separating them is not a matter of preference. It is a maintainability decision. A policy that states the organization enforces multi-factor authentication for all privileged access should remain stable for years. The procedure that describes how MFA is configured in a specific identity provider will change every time the organization updates its tooling. When both live in the same document, every tooling change requires a policy review and approval cycle, which means either the document falls out of date or the approval process becomes a rubber stamp. Neither outcome is useful.
The governance framework for ITSP.10.171 should include, at minimum: an overarching security policy, family-specific policies for each of the seventeen control families, operational procedures that implement those policies, and a rules of behavior document that applies to all users.
Policy vs. Procedure: Why Separation Matters
When policies and procedures live in the same document, every tooling change triggers a full policy review cycle. The result is either documents that fall out of date or an approval process that becomes a rubber stamp. Neither outcome is useful for an operational security program.
Rules of Behavior
ITSP.10.171 requires organizations to establish rules of behavior describing the responsibilities and expected behavior of users with respect to information system security. Users must acknowledge the rules before being granted access, and the rules must be reviewed and updated on a defined frequency.
Rules of behavior are distinct from an acceptable use policy, though they overlap. Where an acceptable use policy focuses on what users are allowed to do with organizational systems, rules of behavior focus on what users are expected to do to protect information and maintain security. This includes responsibilities around handling controlled information, reporting suspected incidents, protecting authentication credentials, and complying with access control requirements.
In practice, rules of behavior work best as a concise, plain-language document that every user reads and signs during onboarding, with an annual re-acknowledgment. The document should be specific enough to be meaningful but short enough that people actually read it.
Why Training Records Matter More Than Training Content
There is a pattern that surfaces during compliance assessments across multiple frameworks, not just CPCSC. Organizations invest significant effort in developing or purchasing training content, completing annual awareness campaigns, and tracking completion rates. Then, when asked to demonstrate role-based training for specific personnel categories, the records either do not exist or show that everyone completed the same generic module.
The issue is not that the training content is bad. It is that the training program was designed around content delivery rather than competency development. From an assessment perspective, a simple record showing that the incident response team received a tabletop exercise on handling breaches involving controlled information is stronger evidence than a 95% completion rate on a vendor-provided phishing awareness course.
Training records should demonstrate three things: coverage (all personnel were trained), relevance (the training was appropriate to the individual's role), and currency (the training occurred within the required timeframe). An assessor reviewing AT controls will pull a sample of personnel from different role categories and trace each person back to their training records. If the system administrator's record shows the same training as the marketing coordinator's, the role-based training requirement is not met.
Common Gaps
No Role-Based Training Program
This is a frequent gap across organizations preparing for CPCSC. Annual security awareness training exists. It might even be good. But there is no differentiated training for system administrators, incident responders, or personnel who handle controlled information. The fix is not complicated, but it does require identifying the role categories that ITSP.10.171 cares about and building or sourcing training content specific to each.
Policy-Procedure Mixing
When policies and procedures live in the same document, one of two things happens. Either the document becomes so long that nobody reads it, or the operational details fall out of date because updating the procedure triggers a full policy review cycle. The result is governance documentation that does not reflect how the organization actually operates, which is a finding during any serious assessment.
Template Policies Without Substance
Some organizations acquire policy templates, whether from a vendor, a consultant, or an online repository, swap in the company name, and distribute them for signature. The documents technically exist, but they do not reflect the organization's actual environment, risk posture, or operational practices. The first time something goes wrong, the gap between what the policy says and what the organization actually does becomes obvious.
Common Pitfall
A policy document should describe what the organization genuinely commits to doing. If the organization does not perform quarterly access reviews, the policy should not claim quarterly access reviews. It is better to have an honest policy with a documented remediation plan than a comprehensive policy that nobody follows.
Governance Without Ownership
The governance framework needs an owner. Not a committee, not a shared responsibility, but a named individual who is accountable for maintaining policies, ensuring training is delivered, tracking records, and updating the framework when the organization's environment changes. Without clear ownership, governance documents drift out of date, training cycles get missed, and the framework becomes an artifact of the last compliance push rather than an operating system for the security program.
Building a Sustainable Governance Program
The mistake that leads to governance failure is treating it as a project with a completion date rather than an ongoing operational function. Building the initial policy set is the easy part. Maintaining it, keeping training current, updating procedures when systems change, and ensuring new personnel are trained before they touch production systems is the ongoing work that actually matters.
A sustainable approach has four elements:
Defined ownership. A single person owns the governance framework and is accountable for its currency. In organizations without a dedicated security team, this often falls to the CTO or IT manager. Under CPCSC, this person should be identified in the system security plan.
Structured document hierarchy. Policies at the top, standards and guidelines in the middle, procedures at the bottom. Each layer changes at a different frequency. Policies might be reviewed annually. Procedures might update monthly. Keeping them separate makes both activities manageable.
Training calendar. Rather than scrambling to complete training before an assessment, build a calendar that schedules awareness training for all users and role-based training for specific personnel categories. Include tabletop exercises for incident responders, configuration management reviews for system administrators, and handling procedures for anyone who touches controlled information.
Record-keeping by design. Training records should be a natural output of the training delivery process, not a retrospective documentation exercise. Whether the organization uses a learning management system, a shared drive with signed acknowledgments, or a spreadsheet, the system should capture who, what, when, and which role category, automatically.
| Element | Purpose | Review Frequency |
| Defined ownership | Single accountable person for the governance framework | Ongoing |
| Document hierarchy | Policies, standards, procedures separated by change frequency | Annually (policies), as needed (procedures) |
| Training calendar | Scheduled awareness and role-based training cycles | Annually |
| Record-keeping | Automated capture of who, what, when, and role category | Continuous |
The governance framework is what makes a security program a program rather than a collection of tools and good intentions. AT is not among the six families expected at Level 1; it applies at Level 2 under the full ITSP.10.171 standard. However, governance practices and training programs support every other control family, making them worth building early regardless of certification level. For organizations pursuing CPCSC certification, the AT controls and governance structure are straightforward to implement if approached deliberately. The risk is treating them as an afterthought and discovering during assessment that the connective tissue does not exist.
Updated April 14, 2026 — Final CPCSC Level 1 Requirements
Are you ready for CPCSC Level 1?
Take the scorecard to find out.
FAQ
Does ITSP.10.171 require role-based training, or just general awareness?
Both. The ITSP.10.171 AT family includes requirements for general security awareness training for all users and role-based training for personnel with assigned security responsibilities. AT is a Level 2 control family (the Government of Canada has not confirmed AT in the Level 1 scope), but organizations targeting Level 2 certification must satisfy both requirements. General awareness alone does not satisfy the standard.
How often does security awareness training need to be delivered?
ITSP.10.171 requires initial training for new users and ongoing training thereafter. The standard does not prescribe a specific frequency, but annual training is the widely accepted minimum for general awareness. Role-based training should be delivered when personnel are assigned new security responsibilities and refreshed at least annually. More frequent training, such as quarterly tabletop exercises for incident responders, strengthens the program and the evidence base.
Can we use an off-the-shelf training platform to meet CPCSC training requirements?
Off-the-shelf platforms are a reasonable starting point for general awareness training, but they rarely cover the role-based training requirements specific to handling controlled information under ITSP.10.171. Most commercial platforms focus on phishing awareness, password hygiene, and general cyber threats. Organizations should plan to supplement vendor-provided content with role-specific training developed internally or sourced from specialized providers.
What is the difference between a security policy and a procedure under ITSP.10.171?
A policy states what the organization commits to doing and at what standard. A procedure describes how specific activities are performed, including system-specific steps, responsible personnel, and operational detail. ITSP.10.171 expects both to exist, and separating them is a practical decision that makes the governance framework easier to maintain as the organization's environment changes.
Next Steps
Organizations preparing for CPCSC certification often build the technical controls first and leave governance and training for the end. That sequence works until the assessment, when the governance framework is what demonstrates that every other control family is operating as intended. Starting with a clear policy structure, a training calendar, and defined ownership costs very little and makes the rest of the program defensible.
If your team is building toward CPCSC and needs help structuring the governance framework or mapping existing controls to ITSP.10.171, we can help.
Ready to Start Your Compliance Journey?
Get a clear, actionable roadmap with our readiness assessment.
About the Author
Former security architect for Bank of Canada and Payments Canada. 20+ years building compliance programs for critical infrastructure.
Ready for CPCSC Level 1?
Score your readiness across the 6 expected control families. Free.
Take the Scorecard