How to read the SOC 2 services market before you scope a vendor: the three layers, the four flavors of consultancy, and the gap between the dashboard and the program.
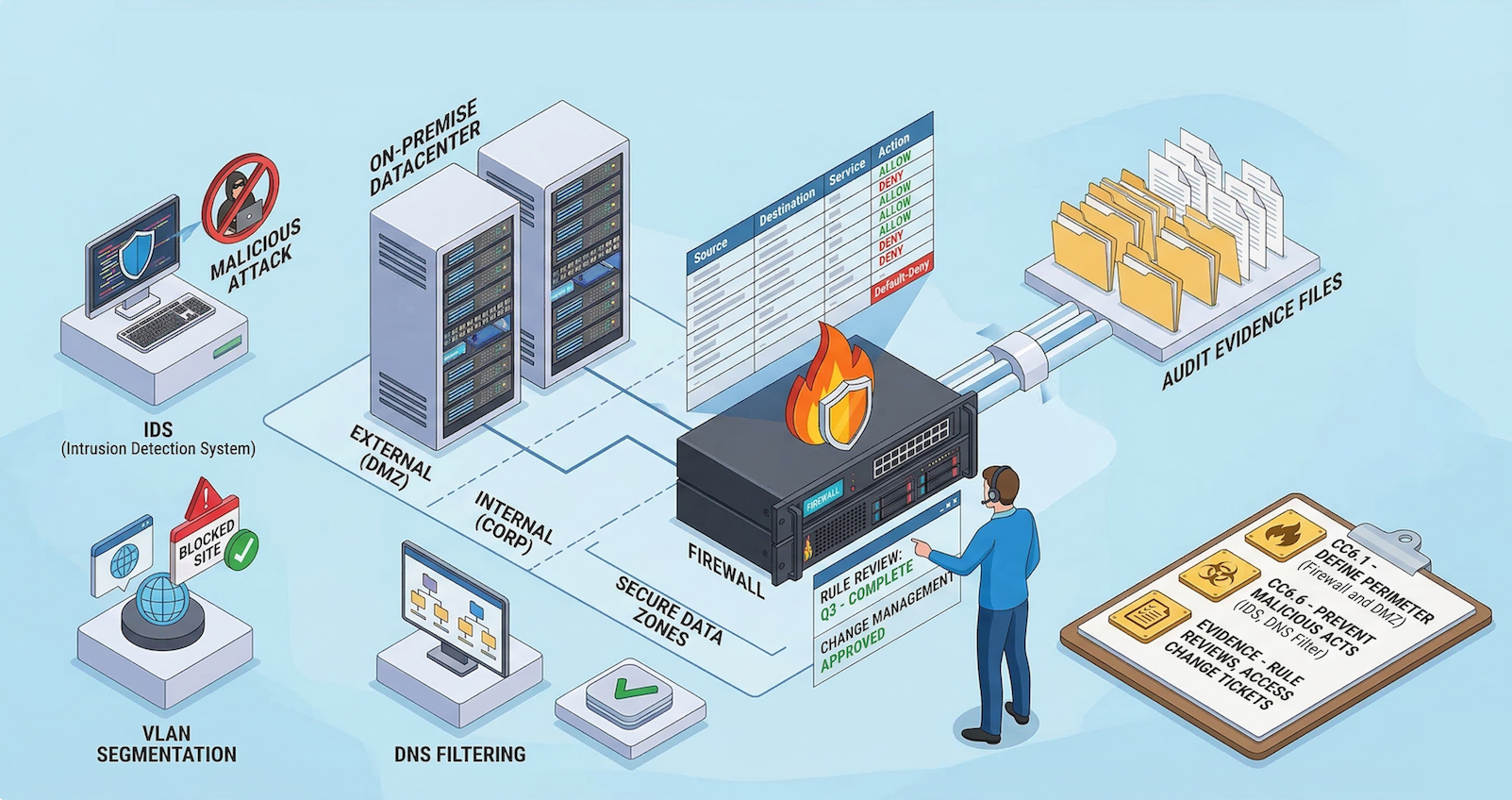
The first slide of the GRC platform looks great. Compliance score: well above 80 percent. Policies uploaded: all of them, green across the board. Evidence collection: green. Then a senior consultant opens the same environment and the picture changes. Most of those policies are not actually assigned to anyone on the workforce. The platform's roster shows roughly 260 people; the company has about 170. The cloud-native detection stack is disabled across the board. Production SSH is open to the public internet. The dashboard is telling the truth about itself. It is not telling the truth about the program.
That gap, between what the platform reports and what an auditor will actually find, is what every Canadian company evaluating SOC 2 services is trying to close. The market for closing it is not flat. It has three distinct layers, and within one of those layers, four very different kinds of firm produce very different outcomes.
This page is the orientation. If you already know what kind of help you need and you want a firm comparison, the top SOC 2 consultants in Canada listicle is the next stop.
Where is your SOC 2 program today?
Take the 5-minute SOC 2 Readiness Scorecard. Get a benchmark against the Trust Services Criteria before you scope a vendor.
Take the ScorecardThe direct answer
There is no single best SOC 2 compliance service in Canada because SOC 2 is not produced by a single service. It is produced by the combination of three things working together: an audit firm that signs the report, a GRC platform that automates evidence collection and tracking, and a consultancy that designs the program, configures the platform, and runs the work the platform cannot run by itself. Most Canadian companies need at least two of the three. Many need all three.
Each layer does work the others cannot legally or practically do. AICPA independence rules prohibit the audit firm from designing the controls it audits. GRC platforms surface what is in their dashboards but cannot make the underlying program real. Consultancies build and operate the program but do not issue the report. The right SOC 2 service is whichever combination of the three matches your infrastructure, your customer base, your regulatory overlay, and how much of the program you want to run yourself.
Within the consultancy layer, four flavors of firm operate in Canada, and they produce meaningfully different outcomes:
- Platform-led shops. Fast, template-driven, configured around a single GRC platform. Best for cloud-native SaaS with simple scope.
- Big consulting firms. Deep benches, regulator-grade documentation, structured around enterprise engagements. Best for multinationals and regulated industries.
- Generalist MSSPs. SOC 2 readiness as a line item alongside managed security operations. Best when SOC 2 is one part of an existing MSSP relationship.
- Expertise-led, engineering-minded multi-framework consultancies. CISSP-led engagements, platform-agnostic, fluent across SOC 2, ISO 27001, ISO 42001, CMMC, CPCSC, and Canadian privacy law. Best for complex environments, hybrid or on-prem infrastructure, and multi-framework programs that have to hold up under enterprise procurement scrutiny. This is where Truvo lives, and we are among the top consultancies in Canada in this category.
The rest of this page unpacks each layer, names the providers buyers actually evaluate, and tells the story of how a program rated above 80 percent compliant by its GRC platform can have multiple critical findings on the first day of a real assessment.
The three layers (and the gap each one closes)
| Layer | What they do | Cannot do | Common Canadian providers |
| Auditors | Sign the SOC 2 report | Design the controls they audit (AICPA independence) | Big 4 (Deloitte, KPMG, PwC, EY); mid-tier (BDO, MNP, Grant Thornton, RSM, Richter); specialist (Prescient Assurance, MHM Professional Corporation) |
| GRC platforms | Automate evidence collection, policy tracking, control mapping, continuous monitoring | Make the underlying program real if it is not already | Vanta, Drata, Secureframe, Scrut, Sprinto, Cocoon, Mycroft.io |
| Consultancies | Design controls, write policies, configure the platform, run the program, manage the audit | Issue the audit report | Four flavors below |
Each layer has its own market, its own pricing model, its own selection logic. Treating them as substitutes for each other is the most common error first-time SOC 2 buyers make.
Layer 1: Auditors (the people who sign the report)
A SOC 2 report is an attestation issued by a licensed CPA firm against the AICPA Trust Services Criteria. That is the definition. Anyone offering you a SOC 2 certification without a CPA firm in the loop is selling you something else.
In Canada, the audit firms shortlisted for SOC 2 work fall into three groups. The Big 4 (Deloitte, KPMG, PwC, EY) cover enterprise engagements and multinationals running SOC 2 alongside SOX, financial audit, or large transformation programs. Mid-tier Canadian firms (BDO, MNP, Grant Thornton, RSM, Richter) cover the mid-market with regional partner relationships and lower fees. Specialist SOC and ISO audit firms like Prescient Assurance and MHM Professional Corporation focus exclusively on cyber and privacy attestation, often at lower cost than Big 4 with comparable rigor for SaaS scope.
The independence rule that catches first-time buyers
AICPA standards prohibit the same firm from designing the controls it audits. If a firm offers you end-to-end SOC 2, read the engagement letter carefully. The readiness work and the audit have to be structurally separated, with different partners and ideally different teams. If they are not, the audit opinion is not defensible.
Cost orientation. Reputable Canadian and US audit firms quote SOC 2 Type II audits between $15,000 and $40,000 CAD for SMB SaaS scope. Multi-category or multi-system scopes push to $50,000 or more. Big 4 audits run higher, $80,000 to $200,000 plus, which is rarely justified outside enterprise contexts.
Layer 2: GRC platforms (the people who automate the dashboard)
GRC platforms are software products, not services. They integrate with your cloud, identity provider, ticketing system, and HR platform; pull evidence on a schedule; map evidence to controls; track policy attestations; and produce a dashboard that shows where the program stands against a chosen framework.
The platforms most Canadian buyers evaluate are Vanta, Drata, Secureframe, Scrut, Sprinto, Cocoon, and Mycroft.io. Each has strengths and rough edges, and each fits a slightly different stack and team shape. The right choice depends on your infrastructure mix, your existing tooling, and how much of the work you want the platform to do versus a consultant to do. If you want a longer read on this specifically, compliance consulting versus GRC platform covers the boundary.
What platforms do well: they make a real program traceable. They turn evidence collection from a quarterly fire drill into a continuous process. They produce the artifacts auditors expect, in the format auditors expect.
What platforms cannot do: make a program real if it is not. The dashboard reports what it can see, and what it cannot see is often where the work actually lives.
When the dashboard is not the program
We were brought in recently for a gap assessment at a healthtech SaaS preparing for HIPAA and GDPR. The company was already running a top-tier GRC platform. The platform's dashboard showed the program well above 80 percent compliant. A few days of real assessment surfaced roughly 30 findings across four themes: about 8 Critical, 14 High, 6 Medium.
Platform vs. Reality
- Policies: All authored on the platform. Most of them not assigned to any workforce member; several unsigned.
- Workforce roster: Platform showed roughly 260 people. Identity provider showed about 220. Operational headcount was about 170.
- Cloud detection: The cloud-native detection and posture stack disabled across the account.
- Network exposure: Production SSH open to the public internet.
- Change management: Roughly 600 of 1,500 sampled pull requests merged without review records. About 40 percent no-review rate.
- Vendor management: Hundreds of OAuth-granted apps in the workspace; data-adjacent vendors without signed agreements in place.
The platform was telling the truth about its own dashboard. It was not telling the truth about the program.
That gap is not a failure of the platform. The platform was doing exactly what it was built to do: track the things it can see. Policy uploads, integration health, attestation completion. The things it cannot see (whether a policy is actually assigned, whether the cloud controls outside its read scope are turned on, whether a pull request was reviewed by a human, whether a vendor has a signed data agreement in place) were never going to surface on a dashboard.
This pattern is not unique to one platform or one client. The same shape shows up in SOC 2 engagements as much as HIPAA, in ISO 27001 work as much as Law 25 work. The platform is shaped to a particular kind of evidence, and the program is shaped to a particular kind of operation. They overlap heavily, but the overlap is not complete. Closing the remainder is a consultancy problem, not a software problem.
Cost orientation. GRC platforms run $5,000 to $25,000 per year for SMB scale, depending on the platform, the framework count, and the integration depth. Some platforms include a partner-channel implementation discount; some do not.
Layer 3: Consultancies (the people who design and run the program)
Consultancies are where the work the platform cannot do gets done. Within Canada, four flavors of consultancy operate in the SOC 2 market. They are not interchangeable, and the price-to-outcome ratio across them varies more than first-time buyers expect.
3a. Platform-led shops
Boutique firms or individual consultants whose practice is structured around implementing a specific GRC platform (Vanta, Drata, Scrut, Secureframe). They move fast, they know one platform deeply, and they are often the cheapest option on the table.
Where they fit. Year-one Type I on a single AWS product, cloud-native SaaS, simple scope, speed-over-depth situations.
Where they break. Type II observation periods on hybrid or on-prem stacks. Multi-framework overlap. Subservice carve-outs. Complex change management. Anything that does not map cleanly into the platform's default catalog tends to get compressed or skipped. Policies are templated, lightly customized, and rarely reflect how the team actually works.
The signal to watch. A bundled package under $15,000 CAD for the full readiness, platform, and audit stack. The math does not leave room for actual program design at that price; you are buying templates and platform configuration.
3b. Big consulting firms
Big 4 advisory practices, large global consulting firms, and the Canadian arms of major US consultancies. Deep benches, regulator-grade documentation, partner-level senior involvement on enterprise accounts.
Where they fit. Enterprises and regulated industries where SOC 2 sits inside a larger transformation program; multinationals running SOC 2 alongside SOX or large compliance programs; public sector and crown corporations with existing Big 4 procurement vehicles.
Where they break. Mid-market and SMB SaaS. Big 4 hourly rates are sustainable for enterprises and crush growing SaaS budgets. Engagement velocity tends to be slow, partner involvement is often limited to the sales call, and the actual delivery is associate-heavy. The audit-firm-and-consultant separation also bites here: if your auditor is the Big 4 firm, your readiness consultant has to be someone else, often another Big 4 firm, doubling the engagement footprint.
3c. Generalist MSSPs and managed security firms
Managed security service providers offering SOC 2 readiness as one line item alongside managed SOC, managed detection and response, vulnerability management, and incident response.
Where they fit. Companies that already have an MSSP relationship for security operations and want to add SOC 2 inside the same vendor footprint. Mid-market enterprises that prefer one vendor across MSSP, MDR, and GRC advisory.
Where they break. SOC 2 practice depth varies widely inside this category, often within the same firm. The compliance team and the operations team are sometimes the same people splitting time, and AICPA framework fluency is uneven. Ask the same scoping questions of an MSSP that you would of a pure-play SOC 2 firm: how many engagements run last year, which auditors managed, which Trust Services Criteria specifically.
3d. Expertise-led, engineering-minded multi-framework consultancies
This is the flavor that is hardest to pin down with a single label, because it does not exist as a productized category in most directory listings. The shape is consistent though. Senior practitioners (CISSP-credentialed, ten-plus years in cybersecurity) running engagements end-to-end. Platform-agnostic, treating the GRC platform as one tool in the stack rather than the methodology. Multi-framework fluency: SOC 2 alongside ISO 27001, ISO 42001, CMMC, CPCSC, HIPAA, PIPEDA, and Quebec Law 25, because the underlying controls overlap heavily and a program-first approach maps frameworks onto a single foundation. Engineering-minded delivery: version-controlled policies, evidence as code, programmatic control mapping, automated drift detection, infrastructure-as-code review.
This flavor practices what the GRC engineering community calls GRC engineering. The term is community-originated, not Truvo-coined; we adopted it because it accurately describes what the work actually looks like when it is done well. Policies stop being Word documents and start being version-controlled artifacts. Evidence collection stops being a quarterly fire drill and starts being a pipeline. Controls stop being a spreadsheet and start being mapped into the systems they govern.
Where they fit. Mid-market Canadian SaaS, fintech, insurance technology, healthtech, defence supply chain, and regulated infrastructure where SOC 2 is a revenue gate and the program has to hold up under enterprise procurement scrutiny. Hybrid and on-prem environments, including colocation, bare metal, and self-hosted SIEM stacks, where automated evidence collection caps at 20 to 30 percent and senior consultant time is the only way through. Multi-framework programs where SOC 2, ISO 27001, ISO 42001, CMMC, or CPCSC are stacking inside a 12 to 24 month window. Companies without a dedicated internal compliance lead that want one accountable partner running the program on a fixed-price subscription rather than stitching together a consultant, a platform vendor, an MSSP, and an auditor separately.
Where they break. Trivially simple scope where a platform-led shop will be faster and cheaper. Companies that already have a deep internal compliance team and just want a contractor for a specific deliverable.
This is where Truvo lives
We are among the top consultancies in Canada in this category. We are not shy about saying so.
Adjacent: security tools that cover specific control families
A handful of security tools are not consultancies and not GRC platforms but cover specific control families that SOC 2 expects evidence for. They show up in scoping calls because they reduce the consulting effort on the control areas they cover.
The most common in the Canadian mid-market is Field Effect, the Canadian-headquartered managed detection and response platform. Field Effect's MDR covers a meaningful portion of the SOC 2 Detect and Respond control family (logging and monitoring, incident response readiness, vulnerability management telemetry) for companies that do not have an internal SOC. It does not replace the rest of the program. It does not write your policies, configure your access reviews, manage your auditor, or build your control inventory. But on the controls it covers, it produces auditor-ready evidence out of the box, which is a real cost saver in scope.
The pattern generalizes. Endpoint detection platforms, identity providers, secrets managers, vulnerability scanners, and PAM tools each cover specific Trust Services Criteria slices. A serious consultant will scope around the tools you already have rather than recommend a clean-sheet stack on day one.
Canadian-specific selection filters
Once you have decided which layers you need and which flavor of consultancy fits, the Canadian context filters the shortlist further. The questions below are the ones US-focused buyer's guides leave out.
PIPEDA and Law 25 overlap. If your company handles personal information about Canadians, the federal Personal Information Protection and Electronic Documents Act applies, and for Quebec data subjects, Quebec Law 25 applies in parallel. SOC 2 does not satisfy PIPEDA and PIPEDA does not satisfy SOC 2, but controls overlap heavily in access management, data handling, breach notification, and retention. A consultant who treats PIPEDA as an afterthought ends up rebuilding the program in year two when a customer asks for privacy alignment.
OSFI B-13 pass-through. If your customers include federally regulated financial institutions, their third-party risk management programs push OSFI B-13 expectations onto you contractually. Those expectations do not map one-to-one to SOC 2 Trust Services Criteria. A consultant who does not understand the OSFI pass-through framework will scope the program too narrowly and fail the first bank vendor review.
Data residency. Canadian enterprise buyers routinely ask whether data stays in Canada. The answer has to live in both your architecture and your SOC 2 scope statement. A consultant experienced with Canadian buyers will anticipate the question and scope the program to answer it directly.
NRC IRAP funding alignment. Companies that have taken IRAP funding can often use SOC 2 consulting spend as eligible expenses under certain program streams. Ask any prospective consultant whether they have supported IRAP documentation for prior clients.
Bilingual documentation. Companies operating in Quebec, selling to Quebec-domiciled customers, or under Law 25's reach may need policies and evidence in both languages. Confirm capability before signing.
On-prem and hybrid infrastructure. Canadian fintech, insurance technology, and government suppliers run non-cloud environments more often than equivalent US SaaS. If any part of your stack lives outside a hyperscaler, ask prospective consultants how many engagements they have run on infrastructure that looks like yours. The answer separates real operators from cloud-only practitioners. SOC 2 scoping for hybrid infrastructure covers this in depth.
Red flags specific to the Canadian market
- A single firm offering readiness, audit, and ongoing attestation under one engagement letter. AICPA independence rules prohibit it. Either the firm is wrong about the structure, or the audit is being run by a partner who cannot sign a clean report on work their own firm designed.
- Readiness quotes under $15,000 CAD all-in. The math does not leave room for program design, policy customization, or auditor management.
- No mention of PIPEDA, Law 25, or OSFI B-13 on a scoping call with a Canadian-based client selling into Canadian customers. Either the consultant has not worked with the Canadian regulatory stack, or they assume you have not.
- Exclusive focus on a single GRC platform. A consultant that only implements one platform is a platform partner regardless of how they describe themselves. Fine for the right scope; not a multi-framework cybersecurity consultancy.
- A senior consultant at the sales call who disappears at kickoff. The shape of the engagement is set by who actually runs it, not who pitches it.
- Refusal to introduce auditor references. Reputable consultants work with multiple audit firms and connect prospective clients with prior engagements on request.
Where Truvo fits
If you are looking for quality, expert-driven, engineering-minded GRC work, the kind that goes beyond the dashboard and stands up under scrutiny in complex environments with hybrid or on-prem infrastructure and multiple overlapping frameworks, that is where Truvo lives. Every engagement is led by a CISSP with ten-plus years in cybersecurity. We treat GRC platforms (Vanta, Drata, Secureframe, Scrut, Sprinto, Cocoon, Mycroft.io) as one tool in the stack, not the methodology. We are platform-agnostic on the recommendation, configure whichever platform fits your stack, and run the work the platform cannot run by itself. We are among the top consultancies in Canada in this category and we are not shy about saying so.
Our practice covers SOC 2, ISO 27001, ISO 42001, CMMC, CPCSC, HIPAA, PIPEDA, and Quebec Law 25, mapped onto a single program rather than rebuilt for each certification. We deliver fixed-price Assess, Build, Operate, and ABO (Assess plus Build plus Operate) engagements, treating the SOC 2 report as the artifact that falls out of an effective security program rather than the program itself. We work routinely with Canadian and US audit firms, including specialist SOC 2 auditors like Prescient Assurance, and we coordinate the auditor relationship through the engagement so the client is not project-managing two vendors during the audit window.
Where Truvo is not the right fit: trivially simple cloud-native scope where a platform-led shop will be faster and cheaper; engagements where the buyer wants only a contractor for a specific deliverable rather than a partner; or contexts where an existing MSSP is already running security operations end-to-end and the SOC 2 work is primarily about attestation evidence on an already-running program.
The SOC 2 consultants in Canada page describes how we work, what the engagement covers, and what we charge. The top SOC 2 consultants in Canada listicle puts us alongside the other firms operating in the Canadian market for direct comparison.
Want a deeper read before scoping a vendor?
The Truvo Special Report, Effective Security First, walks through the program-first methodology used in every engagement on this page. 20 pages, no gate beyond a name.
The underlying pattern
The reason best SOC 2 compliance services in Canada does not have a single answer is that the work is not a single service. It is three layers, with four flavors of consultancy inside one of those layers, and the right combination depends on infrastructure, customer base, regulatory overlay, and how much of the program the company is willing to run itself. The buyer's job is not to find the one best vendor. It is to figure out which combination of layers fits the situation, then choose well within each layer.
The consultancies worth hiring share a trait that has nothing to do with flavor. They treat SOC 2 as the artifact that falls out of an effective security program, not as the program itself. That distinction matters more in year two than in year one, and more in the tenth customer security review than in the first. The dashboard will keep reporting what it can see. The program is what makes the dashboard true.
Frequently asked questions
Do I need a SOC 2 consultant if I already have a GRC platform?
Almost always yes. The platform tracks what it can see, policy uploads, integration health, attestation completion. It cannot make a program real if it is not. The dashboard reports what it can read, not what is operationally true: whether policies are assigned, whether cloud controls outside its read scope are turned on, whether vendors have signed agreements in place, whether code reviews actually happen. A consultant closes the gap between the dashboard and the program. The platform is a force multiplier on real work, not a substitute for it.
What is the difference between a SOC 2 consultant and a SOC 2 auditor?
An auditor is a licensed CPA firm that issues the SOC 2 attestation report. A consultant designs the controls, writes the policies, configures the GRC platform, and gets the program audit-ready. AICPA independence rules prohibit a single firm from doing both, the auditor must be structurally independent of the people who built the controls. Most Canadian buyers need both, separately, with the consultant managing the auditor relationship through the engagement.
How much do SOC 2 compliance services cost in Canada?
First-year totals for SMB Canadian SaaS typically run between CAD$40,000 and $85,000 across all three layers. Audit fees from reputable Canadian and US firms are CAD$15,000 to $40,000 for SOC 2 Type II on SMB scope. GRC platforms run $5,000 to $25,000 per year for SMB scale. Consultancies run from CAD$20,000 for tightly scoped engagements up to $75,000 plus for enterprise scope. Big 4 advisory pushes total spend to $80,000 to $200,000 plus, which is rarely justified outside enterprise contexts. Bundled packages under $15,000 for the full stack should raise a flag; the math does not leave room for actual program design at that price.
Can a Canadian CPA firm do both SOC 2 readiness and the audit?
Not on the same engagement. AICPA standards prohibit a single firm from designing the controls it audits. Some larger Canadian CPA firms offer both services through structurally separated advisory and attestation arms with different partners, but you have to confirm in the engagement letter which partner is signing the audit and which is running the readiness. The two have to be independent for the audit opinion to be defensible. The cleaner pattern is to keep the readiness consultant and the audit firm fully separate.
Should I pick a platform-led shop, an MSSP, or an expertise-led consultancy?
Depends on scope and infrastructure. Platform-led shops fit cloud-native SaaS with simple year-one Type I scope where speed matters and the GRC platform's default catalog covers most of the work. Generalist MSSPs fit when SOC 2 sits inside an existing managed-security relationship and the buyer wants one vendor across operations and compliance. Expertise-led, engineering-minded consultancies fit complex environments, hybrid or on-prem infrastructure, multi-framework programs, mid-market and enterprise scope where the program has to hold up under enterprise procurement scrutiny. The wrong match shows up in year two when the platform-shaped program does not survive an audit it was not designed for.
Is managed compliance (compliance as a service) available in Canada?
Yes. Several Canadian consultancies, Truvo included, offer managed compliance as an annual subscription that bundles program design, ongoing operation, audit management, and (optionally) a GRC platform license and annual penetration test under one fixed price. Truvo calls this offering ABO (Assess plus Build plus Operate). The model fits companies without a dedicated internal compliance lead, where the alternative is the CTO running the program on spare time until it breaks. Subscriptions in the Canadian market typically start around CAD$45,000 annually for SMB SaaS with single-framework scope.
Should a Canadian SaaS hire a Canadian or a US SOC 2 consultant?
Less about geography than fit with infrastructure, regulatory overlay, and customer base. US firms work with Canadian clients routinely and Canadian firms work with US clients routinely. The deciding factors are usually experience with the Canadian regulatory stack (PIPEDA, Law 25, OSFI B-13), hybrid or on-prem infrastructure if applicable, and bilingual documentation capability for Quebec-facing companies. Canadian consultants are more likely to have the regulatory and bilingual fluency. Both populations include firms with on-prem experience.
What does SOC 2 not cover that PIPEDA or Law 25 still requires?
SOC 2 is a US security and trust framework, not a Canadian privacy law. PIPEDA and Law 25 add specific obligations around consent, breach notification timelines, data residency, automated decision-making transparency, deletion rights, and bilingual documentation that SOC 2 does not address. Controls overlap heavily in access management, data handling, and retention, but the privacy frameworks have unique requirements (Law 25's automated decision-making disclosure, mandatory breach notification timelines, data portability) that SOC 2 simply does not speak to. A Canadian-facing program needs both, mapped onto a single foundation rather than rebuilt twice.
Further reading
- Top SOC 2 consultants in Canada: the firm-by-firm comparison companion piece.
- SOC 2 consultants in Canada: Truvo's primary Canadian SOC 2 service page.
- SOC 2 for bare metal and on-prem infrastructure: the service page covering colocation, hybrid, and physical-infrastructure SOC 2 work.
- How to choose a SOC 2 consultant: the interview-process companion piece.
- Compliance consulting versus GRC platform: why the platform-only model leaves the program incomplete.
- SOC 2 Trust Services Criteria guide: a reference walkthrough of the AICPA TSC structure used in every audit.
- SOC 2 vs ISO 27001: shared efficiencies: when stacking SOC 2 with ISO 27001 actually saves money.
- SOC 2 scoping for non-SaaS and hybrid infrastructure: scoping decisions for environments that fall outside the cloud-native default.
- The Effective Security First report: the program-first methodology in long form.
Outbound references:
- AICPA Trust Services Criteria (2017, with revisions): the source standard for SOC 2 reporting. aicpa-cima.com
- AICPA SSAE 18 (now AT-C 105 and AT-C 205): the attestation standards that govern SOC 2 reports.
- CPA Canada: the Canadian professional body for CPA audit firms issuing SOC 2 attestations. cpacanada.ca
- NIST Cybersecurity Framework 2.0: the program-level reference Truvo uses to align controls across SOC 2, ISO 27001, and CMMC. nist.gov/cyberframework
Ready to Start Your Compliance Journey?
Get a clear, actionable roadmap with our readiness assessment.
About the Author
Former security architect for Bank of Canada and Payments Canada. 20+ years building compliance programs for critical infrastructure.
How Ready Are You for SOC 2?
Score your security program in under 5 minutes. Free.
Take the Scorecard